
Key Points :
- X plans to automatically lock accounts that post about crypto for the first time
- Initiative led under Elon Musk and product head Nikita Bier
- Targets phishing-driven account takeovers and crypto scam promotions
- Estimated to reduce scam incentives by up to 99%
- Raises broader questions about platform responsibility, including criticism toward Google
- Signals a new era of behavioral security models across social platforms
- Strong implications for crypto adoption, compliance, and user trust
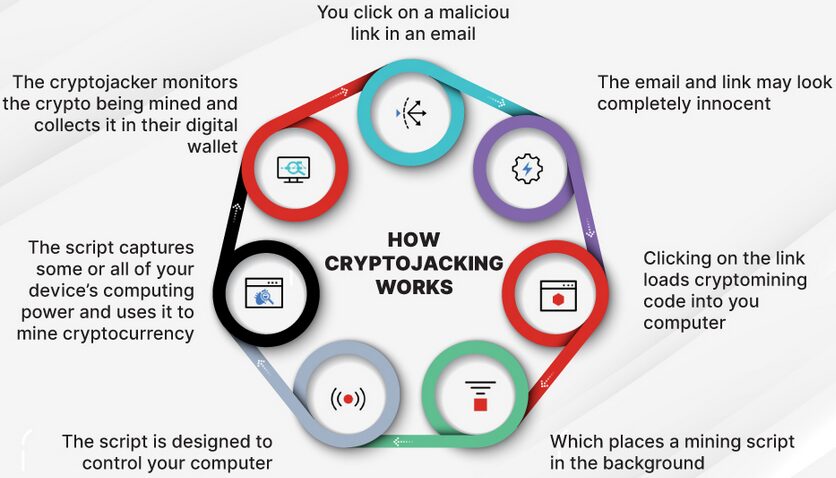
Crypto Scam Lifecycle on Social Platforms (Image below)
Introduction: When Social Media Becomes the Weakest Link in Crypto Security
The rapid expansion of cryptocurrency markets has created not only unprecedented financial opportunities but also a parallel surge in sophisticated cybercrime. Social media platforms—particularly X—have become a central battlefield where legitimacy, influence, and fraud collide.
In a decisive move, X is preparing to introduce an automatic account-locking feature aimed specifically at crypto-related scams. The feature is simple in concept but powerful in implication: if an account that has never previously posted about cryptocurrency suddenly does so, it will be automatically locked until additional authentication is completed.
This represents a shift from reactive moderation to proactive behavioral security—something the crypto ecosystem has long needed.
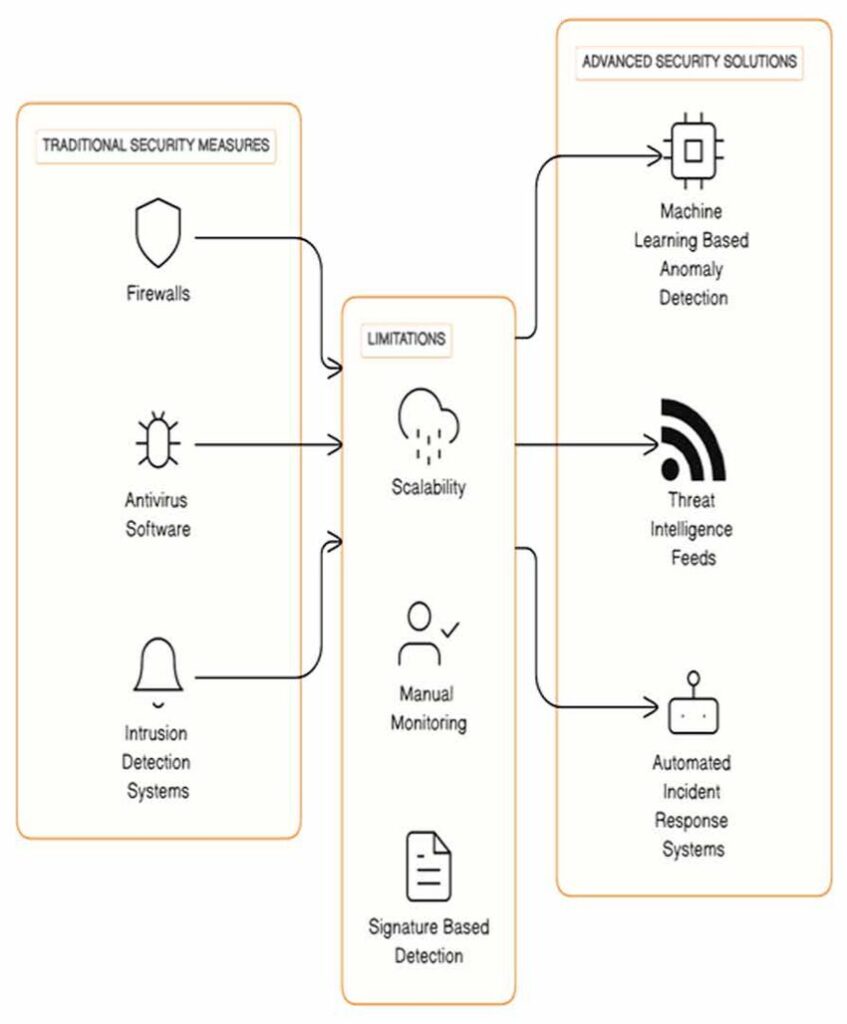
The Mechanism: Behavioral Anomaly as a Security Trigge
How It Works
According to statements from Nikita Bier, the system analyzes posting history. When an account suddenly deviates—specifically by posting about crypto for the first time—it is flagged as potentially compromised.
Instead of waiting for reports or damage, the system:
- Detects anomaly (first-time crypto post)
- Automatically locks the account
- Requires additional authentication
- Restores access only after verification
This is not content moderation—it is behavioral anomaly detection.
Why This Matters
Traditional security systems rely on:
- Password strength
- IP monitoring
- Device fingerprinting
However, attackers increasingly bypass these through phishing, especially targeting 2FA systems. By shifting focus to behavior, X introduces a fundamentally different security layer.
Before vs After Security Model (Image below)
The Real Threat: Phishing + Social Engineering
Case Study Behind the Feature
The announcement was triggered by a real-world incident where:
- A user received a fake copyright infringement email
- The email led to a realistic phishing login page
- Attackers captured both password and 2FA code
- The account was hijacked
- Scam crypto promotions were posted
This pattern is not isolated—it is systemic.
The Weak Point: Human Trust
Even sophisticated users fall victim because:
- Emails mimic legitimate services
- Login pages are indistinguishable
- 2FA is intercepted in real-time
This exposes a harsh truth:
Security systems that rely solely on user vigilance will always fail at scale.
Phishing Attack Flow (Image below)
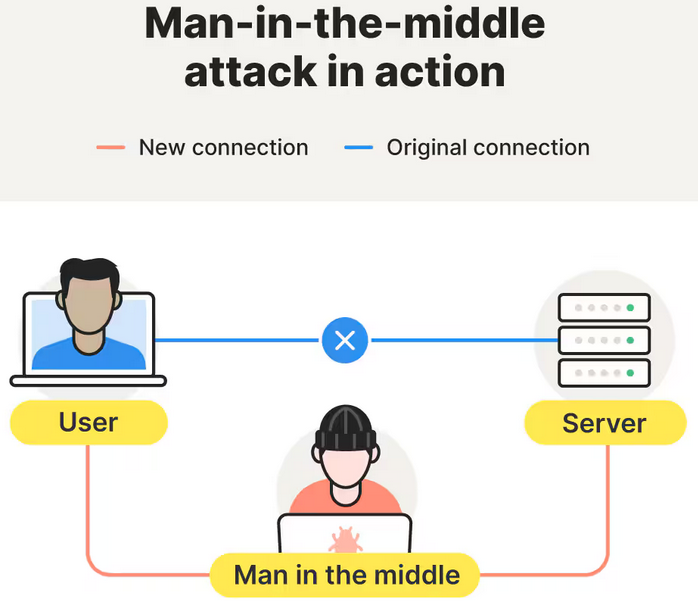
Beyond X: A Signal to the Entire Tech Industry
Indirect Criticism of Google
Bier also pointed out that phishing emails continue to proliferate, suggesting insufficient mitigation by email providers such as Google.
This highlights a systemic issue:
- Email platforms allow phishing entry
- Social platforms become exploitation surfaces
- Crypto becomes the monetization layer
Security failures are interconnected across ecosystems.
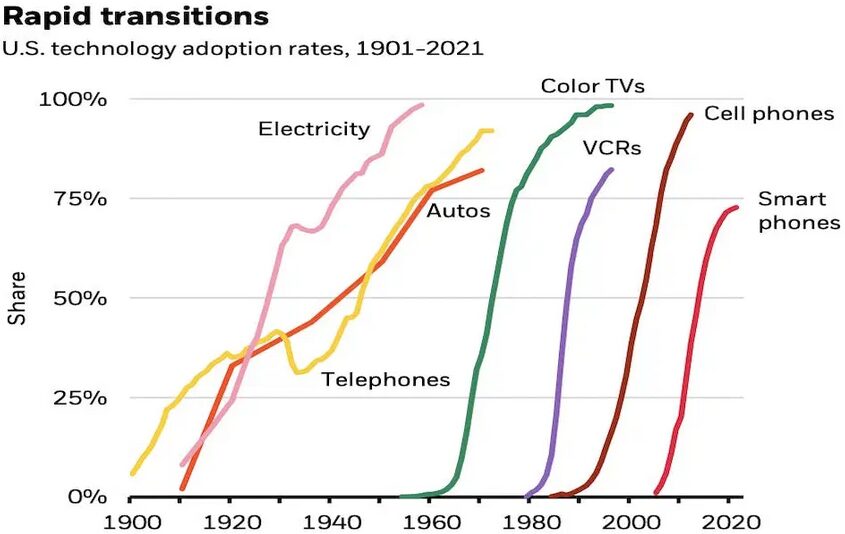
Market Impact: Why This Matters for Crypto Investors
1. Trust is Infrastructure
Crypto adoption is no longer limited by technology—it is limited by trust.
Features like this:
- Reduce perceived scam risk
- Encourage retail participation
- Support institutional entry
2. Compliance Alignment
This model aligns with regulatory expectations:
- Fraud prevention
- User protection
- Behavioral monitoring
It mirrors financial industry practices such as:
- Transaction anomaly detection
- AML risk scoring
3. Platform Risk Becomes Investment Risk
Investors must now consider:
- Which platforms are secure
- Which ecosystems protect users
- Which networks reduce fraud vectors
Security is alpha.
Impact on Crypto Adoption Curve (Image below)
Strategic Insight: The Rise of “Behavior-Based Security”
This move reflects a broader trend:
From Identity → Behavior
Old model:
- Verify who you are
New model:
- Verify how you behave
This is critical for:
- Decentralized finance (DeFi)
- Non-custodial wallets
- On-chain identity systems
Your behavior becomes your security signature.
Opportunities for Builders and Investors
1. Security Layer Startups
New opportunities in:
- Behavioral analytics engines
- On-chain anomaly detection
- AI-driven fraud prevention
2. Wallet UX Innovation
As you are designing non-custodial wallets (like your “dzilla Wallet”), this trend is directly relevant:
- Add behavioral flags
- Detect abnormal transactions
- Trigger step-up authentication
3. Social + Crypto Integration
Future platforms will likely:
- Integrate wallet + identity + social graph
- Monitor behavioral patterns across layers
- Prevent fraud before execution
Conclusion: A Small Feature with Systemic Impact
What appears to be a simple rule—locking accounts on first-time crypto posts—is actually a major architectural shift in how digital trust is enforced.
Under Elon Musk, X is experimenting with a model that:
- Treats behavior as a security signal
- Moves enforcement upstream (before damage occurs)
- Reduces scam profitability dramatically
If successful, this approach will not remain isolated.
It will expand into:
- Financial platforms
- Wallet infrastructure
- Blockchain protocols
And ultimately redefine how trust is built in the digital economy.

