
Key Points :
- Japan’s Financial Services Agency (FSA) has declared that cold wallets alone are no longer sufficient to protect crypto assets.
- A mandatory Cyber Security Self-Assessment (CSSA) framework will be introduced for all exchanges.
- Threat-Led Penetration Testing (TLPT) will be conducted across selected operators in 2026.
- Cyber threats are shifting from direct private key theft to indirect, supply-chain, and social engineering attacks.
- A coordinated model of self-help, mutual aid, and public-sector intervention is now the foundation of crypto security policy.
Introduction: A Structural Shift in Crypto Security Thinking
On April 3, 2026, Japan’s Financial Services Agency (FSA) published a landmark policy titled “Initiatives for Strengthening Cybersecurity in Crypto Asset Exchange Services.” While regulatory updates in crypto are common, this one stands out for a critical reason: it fundamentally reframes how digital asset security should be understood.
For years, cold wallets—offline storage mechanisms—have been widely regarded as the gold standard for safeguarding crypto assets. However, the FSA has now explicitly stated that reliance on cold wallets alone is no longer sufficient. This marks the first time a major regulator has formally acknowledged the limitations of what was once considered the industry’s strongest defense.
This shift is not theoretical. It reflects a rapidly evolving threat landscape where attackers are no longer targeting just private keys but entire ecosystems—human behavior, software dependencies, and third-party infrastructure.
For investors, builders, and institutions seeking new revenue opportunities and practical blockchain applications, this policy signals something deeper: security is becoming the central competitive differentiator in crypto infrastructure.
The End of “Cold Wallet Absolutism”
Why Cold Wallets Are No Longer Enough
Historically, cold wallets were seen as nearly impenetrable because they are disconnected from the internet. Exchanges often stored the majority of user funds in such wallets to mitigate hacking risks.
However, recent incidents have demonstrated that attackers are no longer attacking storage—they are attacking processes and people.
Examples include:
- Social engineering attacks targeting employees
- Compromise of development environments
- Supply chain attacks via open-source dependencies
- Breaches of third-party vendors
The FSA’s position is clear:
Security must extend beyond asset storage to end-to-end operational integrity.
This aligns with global developments seen in incidents affecting platforms connected to ecosystems like Ethereum and Bitcoin, where vulnerabilities increasingly originate outside core wallet infrastructure.
Evolution of Attack Vectors: From Direct Theft to Ecosystem Compromise
From Private Keys to Indirect Attacks
Previously, most crypto breaches involved direct theft of private keys. Today, attackers are more sophisticated.
They now exploit:
- Credential harvesting via phishing and impersonation
- Vendor vulnerabilities through outsourced infrastructure
- Software supply chain attacks, including malicious code injected into widely used libraries
One notable global trend is the rise of attacks targeting open-source ecosystems. A compromised JavaScript package, for example, can cascade into thousands of applications—a risk particularly relevant to Web3 development stacks.
This evolution reflects a broader cybersecurity principle:
The weakest link is no longer cryptography—it is operational complexity.
Global Crypto Attack Surface Evolution (2018–2026)
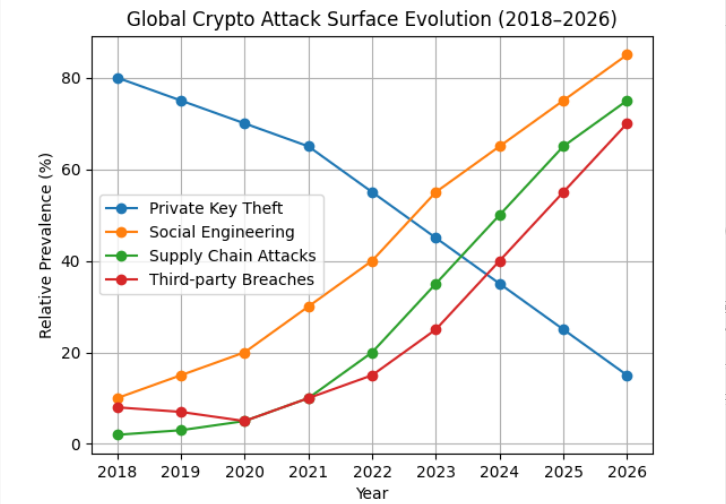
Description:
A line chart showing the decline in direct private key theft vs. the rise in social engineering, supply chain attacks, and third-party breaches.
Three-Pillar Framework: Self, Mutual, and Public Defense
The FSA introduces a structured response model built on three pillars:
1. Self-Help (Individual Responsibility)
Each exchange must strengthen its internal security posture through:
- Mandatory CSSA (Cyber Security Self Assessment)
- Alignment with financial cybersecurity guidelines
- Enhanced governance, including:
- Defined authority for security officers
- Stronger external audit requirements
- Strict vendor security standards
This approach forces exchanges to quantify and benchmark their own weaknesses, a critical step toward institutional maturity.
2. Mutual Aid (Industry Collaboration)
Security is no longer a competitive secret—it is a shared necessity.
Key initiatives include:
- Participation in JPCrypto-ISAC
- Strengthening of self-regulatory bodies like Japan Virtual and Crypto assets Exchange Association
- Continuous information sharing on threats and vulnerabilities
This mirrors global movements such as ISAC frameworks in traditional finance, where threat intelligence sharing significantly reduces systemic risk.
3. Public Support (Government Intervention)
The FSA will actively participate through:
- Threat-Led Penetration Testing (TLPT)
- National cyber exercises such as Delta Wall
- International research collaborations
TLPT, in particular, is a game-changer. Unlike standard penetration testing, TLPT simulates real-world attacker behavior, testing not just systems but also:
- Human response
- Incident detection
- Organizational coordination
TLPT Operational Flow
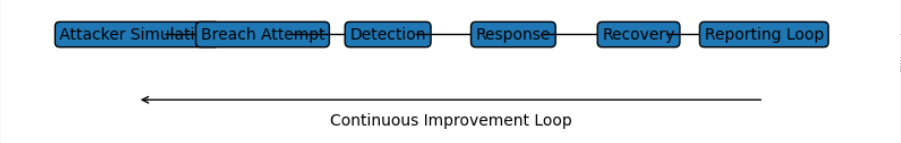
Description:
A flow diagram showing attacker simulation → breach attempt → detection → response → recovery → reporting loop.
Why This Matters: National Security and Capital Protection
The FSA highlights an often overlooked dimension:
crypto security is not just about user protection—it is about national economic security.
There is increasing evidence that state-sponsored actors are involved in crypto attacks, using stolen assets as a source of foreign currency.
This elevates crypto cybersecurity into a geopolitical issue, similar to:
- Banking infrastructure protection
- Energy grid security
- Telecommunications resilience
For countries like Japan, failure to secure crypto infrastructure could lead to:
- Capital outflows
- Loss of trust in financial systems
- Strategic vulnerabilities
Global Context: Convergence with Institutional Crypto Adoption
Japan’s move is not isolated. It aligns with broader global trends:
- Institutional entry into crypto markets (e.g., ETFs, custody services)
- Growth of stablecoins and tokenized deposits
- Integration with traditional financial systems
As institutions enter the space, expectations shift from “startup-grade security” to bank-grade resilience.
This is particularly relevant for hybrid platforms and architectures—like those combining centralized UX with decentralized execution (similar to your XXI Network model)—where:
- Custody
- Execution
- Compliance
- Infrastructure
are all interconnected.
Hybrid Exchange Architecture Risk Layers
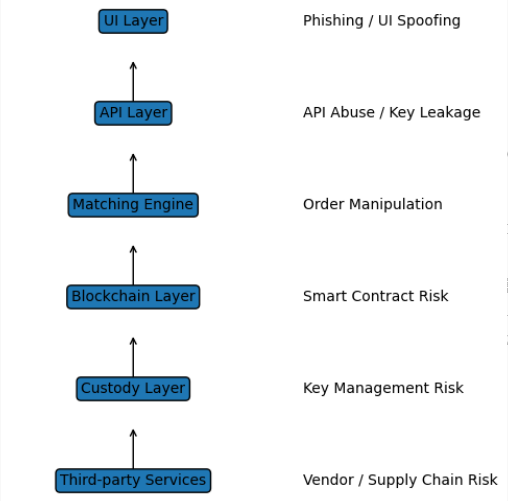
Description:
Layered diagram showing UI → API → Matching Engine → Blockchain → Custody → Third-party services, with risk points highlighted.
Opportunities for Builders and Investors
For readers seeking new crypto assets, revenue opportunities, and practical applications, this regulatory shift opens several strategic directions:
1. Security as a Service (SecaaS)
Demand for:
- TLPT providers
- CSSA compliance tools
- Real-time threat monitoring systems
will surge.
2. Compliance-Native Infrastructure
Projects that embed:
- Auditability
- On-chain transparency
- Regulatory reporting
will gain institutional adoption.
3. Decentralized Yet Compliant Architectures
Hybrid models—like:
- On-chain settlement
- Off-chain UX
- Integrated KYC/AML
will become the standard.
4. Supply Chain Security Solutions
Expect growth in:
- Dependency monitoring tools
- Smart contract auditing platforms
- Developer environment security




