Main Points :
- If sufficiently powerful quantum computers emerge, up to 7 million BTC (approximately $440 billion) could be vulnerable to cryptographic attacks.
- This amount may include around 1 million BTC attributed to Satoshi Nakamoto, currently untouched.
- The Bitcoin community is divided between:
- Preserving strict neutrality and immutability—even if vulnerable coins are stolen.
- Intervening via protocol changes, such as freezing, burning, or migrating exposed coins to quantum-resistant addresses.
- Some researchers warn that cryptographic break timelines may be shortening.
- Others argue the threat remains distant and can be addressed through gradual engineering upgrades rather than radical governance shifts.
1. The Quantum Threat: Why 7 Million BTC Could Be at Risk

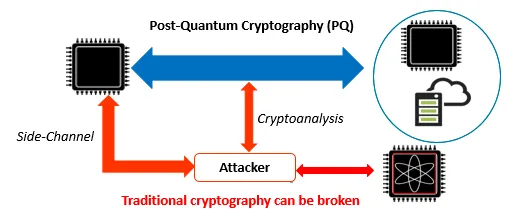
Bitcoin’s security depends primarily on elliptic curve cryptography (ECDSA over secp256k1) and SHA-256 hashing. Under classical computing assumptions, these are secure. However, quantum computing introduces theoretical attack vectors through:
- Shor’s Algorithm (breaks ECDSA by deriving private keys from public keys)
- Grover’s Algorithm (weakens hash security quadratically)
If a quantum computer with sufficient stable qubits (likely in the millions of logical qubits) becomes operational, any Bitcoin address whose public key has been revealed on-chain could potentially be compromised.
Researchers estimate that as much as 7 million BTC are in addresses where public keys are already exposed—either due to reuse or historical transaction patterns. At a hypothetical market price of approximately $63,000 per BTC, that represents roughly:7,000,000×$63,000≈$441,000,000,000
That is about $440 billion at risk.
Among those coins are roughly 1 million BTC attributed to Satoshi Nakamoto, untouched since the early days of Bitcoin. If quantum attackers could derive those private keys, the symbolic and economic shock would be immense.
2. Where the Real Vulnerability Lies
Not all Bitcoin is equally vulnerable.
- P2PK (Pay-to-Public-Key) early addresses are exposed immediately.
- P2PKH (Pay-to-Public-Key-Hash) only reveal the public key when funds are spent.
- Unspent coins in hashed form are currently safe until moved.
Thus, the highest risk lies in:
- Reused addresses
- Early-era coins
- Dormant addresses with revealed public keys
From an investor perspective, this introduces a new classification:
| Category | Quantum Risk Level |
|---|---|
| Fresh P2PKH, never spent | Low (currently protected) |
| Address reuse | Moderate |
| Early P2PK outputs | High |
| Satoshi-era mined coins | High |
This nuance is crucial. The “$440 billion at risk” headline does not mean the entire Bitcoin supply is immediately breakable—but it highlights structural exposure.
3. The Governance Divide: Freeze or Preserve Immutability?

The deeper issue is philosophical.
Camp 1: Preserve Immutability
This faction argues:
- Bitcoin’s neutrality must be absolute.
- Protocol changes to “freeze” coins undermine censorship resistance.
- If quantum attackers steal vulnerable coins, it is a market event—not a governance failure.
- Engineering upgrades (quantum-resistant signature schemes) should be introduced gradually, but without confiscation or burning.
In this view, altering ownership retroactively breaks the core social contract.
Camp 2: Active Intervention
This group argues:
- Allowing $440 billion to be stolen would destabilize the network.
- Preemptively freezing or migrating vulnerable coins protects users.
- A quantum emergency fork could move funds to post-quantum addresses.
- Protecting Satoshi’s coins may be critical to maintaining symbolic stability.
This is not just technical—it is political. It tests whether Bitcoin is:
- A rigid protocol
- Or an adaptable monetary network
For readers interested in governance models and blockchain applications, this debate mirrors larger questions about decentralized autonomy vs. managed resilience.
4. Is the Threat Imminent?
Recent academic work suggests improvements in quantum error correction and qubit coherence are accelerating.
Major players such as:
- IBM
- IonQ
- Rigetti
have announced scaling roadmaps aiming toward thousands—and eventually millions—of physical qubits.
However, experts note:
- Breaking ECDSA likely requires millions of logical qubits, not just physical ones.
- Error correction overhead is enormous.
- Current machines remain far from this threshold.
Many engineers believe:
- The threat is real.
- But likely 10–20 years away.
- Migration paths can be engineered gradually.
This creates a strategic window.
5. Engineering Pathways: Post-Quantum Bitcoin
Potential upgrade paths include:
1. Soft Fork Introducing Post-Quantum Signatures
- Lattice-based cryptography (e.g., CRYSTALS-Dilithium)
- Hash-based signatures (e.g., SPHINCS+)
2. Hybrid Address Formats
Allowing:
- Classical ECDSA
- Post-quantum signature
- Or both
3. Gradual Incentivized Migration
Users voluntarily move coins to new address formats before quantum risk materializes.
This preserves immutability while increasing resilience.
For builders and wallet developers (especially those working on non-custodial architectures), early quantum-resistant support could become a competitive advantage.
6. Market Implications: Volatility, Opportunity, and New Assets
The quantum narrative introduces several market dimensions:
A. Narrative Risk Premium
Markets may begin pricing in quantum risk even before technical viability.
B. Rise of Quantum-Resistant Blockchains
New chains marketing post-quantum cryptography could attract capital.
C. Security Infrastructure Tokens
Projects focused on:
- Cryptographic upgrades
- Secure key management
- Quantum monitoring systems
may see new demand.
D. Institutional Hedging Behavior
ETFs and custodians may demand proof of quantum migration pathways before long-term allocation.
This shifts the narrative from pure speculation to infrastructure robustness.
7. Strategic Takeaways for Investors and Builders
For those seeking new revenue streams or practical blockchain applications:
- Monitor post-quantum cryptography developments.
- Evaluate address reuse exposure in portfolio assets.
- Consider diversification into security-focused crypto infrastructure.
- Watch governance debates—fork risk equals market volatility.
- Support wallet-level cryptographic flexibility.
The quantum threat is not merely a technical curiosity—it is a structural stress test.

