
Main Points :
- Elon Musk warns that future quantum computers could unlock even lost crypto wallets
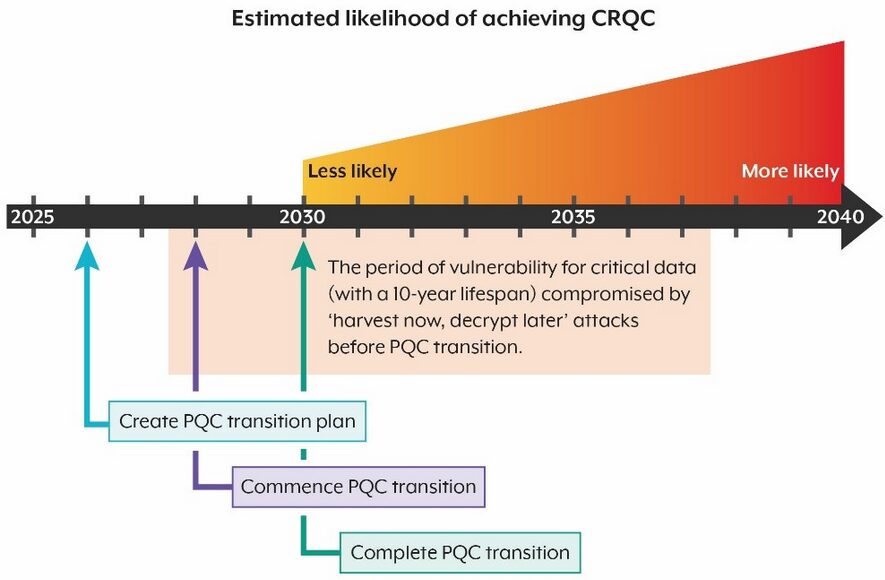
- Google accelerates post-quantum cryptography (PQC) migration timeline to 2029
- Quantum breakthroughs may reduce resources needed to break ECC-256 by ~20x
- “Harvest now, decrypt later” attacks already pose a real risk
- Bitcoin and Ethereum face structural vulnerabilities without upgrades
- The transition to quantum-resistant cryptography is now a strategic urgency, not a theoretical discussion
1. Elon Musk’s Warning: A Joke That Isn’t Funny
Elon Musk recently joined a discussion on X (formerly Twitter) about the risks quantum computing poses to cryptocurrencies such as Bitcoin. In a characteristically ironic tone, he remarked:
“On the bright side, you might be able to access wallets if you forgot your password.”
At first glance, the statement sounds humorous. However, the implication is deeply serious. Musk is pointing out a future where cryptographic protections—currently considered unbreakable—may become obsolete.
This is particularly alarming because Bitcoin’s security relies on elliptic curve cryptography (ECC), specifically ECC-256. If quantum computers can break this system, private keys could be derived from public keys, effectively compromising wallets.
Musk also referenced analysis from his AI chatbot, Grok, suggesting that the timeline for such breakthroughs may be closer than previously assumed.
2. Google’s Accelerated Timeline: Why 2029 Matters
Google has significantly shifted the conversation by advancing its internal deadline for transitioning to quantum-resistant systems to 2029.
This does not mean Google believes quantum computers will definitively break encryption by that year. Rather, it reflects a precautionary principle:
Preparation must be completed before the threat materializes.
According to Google’s research:
- ECC-256 could potentially be broken in minutes
- Fewer than 500,000 physical qubits may be sufficient
- Required computational resources have been reduced by approximately 20x compared to previous estimates
This is not a minor improvement—it represents a fundamental shift in feasibility.
Quantum Threat Timeline (Generated Chart)
3. The Real Risk: “Harvest Now, Decrypt Later”
One of the most critical concepts highlighted in recent research is the “harvest now, decrypt later” strategy.
This attack model works as follows:
- Encrypted blockchain data is collected today
- It is stored indefinitely
- Once quantum computers mature, the data is decrypted
This means the threat is already active, even if quantum computers are not yet capable of breaking encryption.
For cryptocurrencies, this creates a unique vulnerability:
- Public keys are exposed on-chain after transactions
- These keys could be harvested today
- Future quantum attacks could retroactively compromise funds
This is especially relevant for dormant wallets, including early Bitcoin addresses.
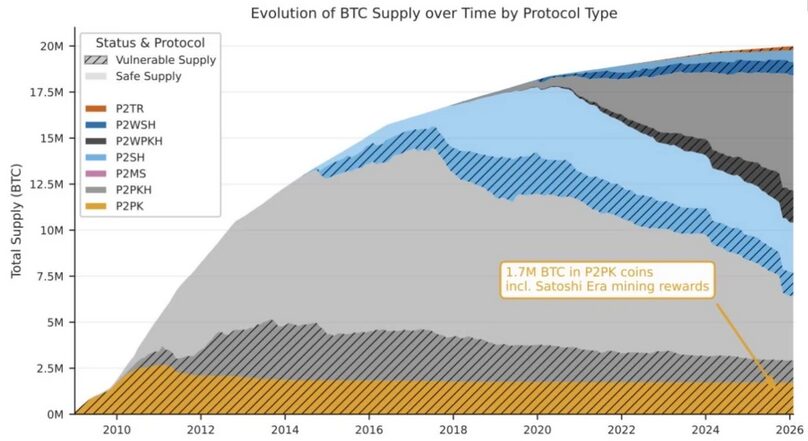
4. Structural Vulnerabilities in Bitcoin and Ethereum
Bitcoin
Bitcoin faces several structural risks:
- Long block times slow protocol upgrades
- Legacy addresses expose public keys after use
- Large amounts of dormant BTC remain vulnerable
Estimates suggest that over $150 billion worth of Bitcoin could be at risk if quantum attacks become viable.
Ethereum
Ethereum has more flexibility due to its programmable nature:
- Easier migration to new cryptographic schemes
- Smart contract-based upgrades
- Active research into PQC integration
However, Ethereum is not immune. Any exposed public key system is inherently at risk.
5. Timeline: When Could Quantum Break Crypto?
Based on combined expert analysis, including projections referenced by Musk’s Grok:
| Scenario | Estimated Timeline |
|---|---|
| Optimistic (fast progress) | 2028–2029 |
| Consensus (most experts) | Early 2030s |
| Conservative | Mid–late 2030s |
This timeline aligns closely with Google’s 2029 migration target.
The key takeaway is not the exact year—but the narrowing window for preparation.
Cryptography vs Quantum Capability Curve
6. Market Implications: Risk, Opportunity, and Strategy
Risk
- Sudden loss of trust in legacy cryptography
- Massive fund exposure from compromised wallets
- Regulatory pressure on exchanges and custodians
Opportunity
For forward-looking investors and builders, this shift creates new opportunities:
- Post-quantum blockchain protocols
- Quantum-resistant wallet infrastructure
- Hybrid systems combining classical and PQC security
Projects focusing on quantum-safe cryptography could become a major investment theme.
7. Strategic Response: What Should Be Done Now
For developers and institutions:
- Begin integrating PQC algorithms (e.g., lattice-based cryptography)
- Design migration paths for existing wallets
- Implement key rotation and address reuse avoidance
For investors:
- Evaluate exposure to legacy chains
- Monitor PQC adoption timelines
- Identify early-stage quantum-resistant projects
For regulators:
- Set migration standards
- Require disclosures on quantum risk
- Encourage industry-wide coordination
Conclusion: The Clock Has Already Started
The quantum threat is no longer theoretical. It is a timeline problem.
Elon Musk’s ironic remark captures the paradox:
The same technology that could recover lost wallets could also destroy the security foundation of digital assets.
Meanwhile, Google’s 2029 deadline signals a clear industry direction:
Act before it is too late.
For the cryptocurrency ecosystem, this is not just a technical upgrade—it is a generational shift.
The winners of the next decade will not only be those who build scalable systems or capture liquidity, but those who anticipate and survive the quantum transition.

