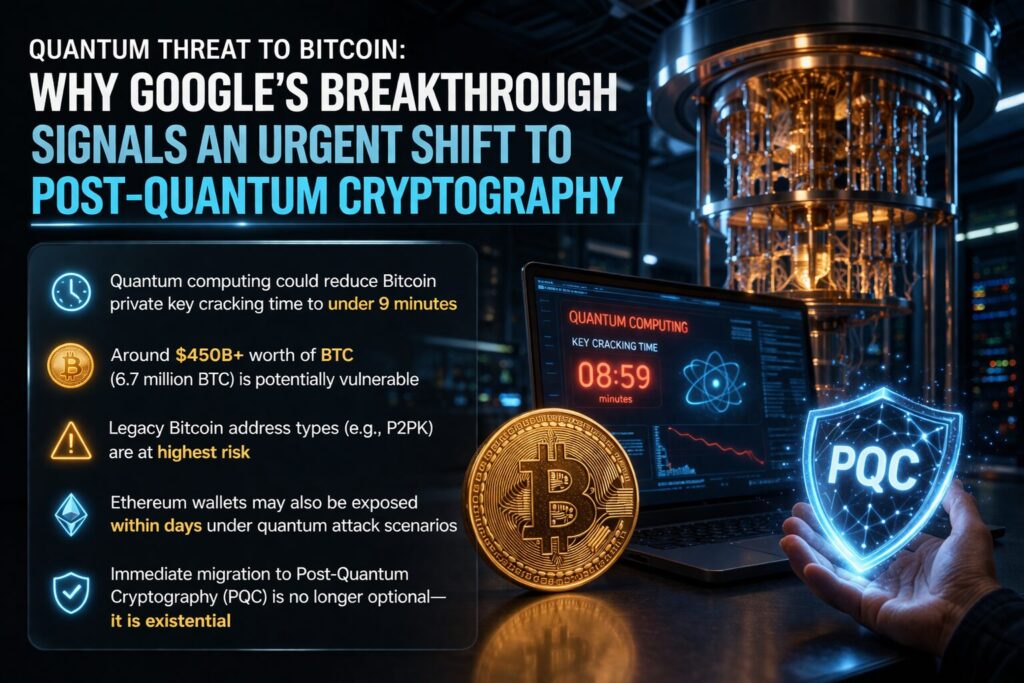
Key Takeaways :
- Quantum computing could reduce Bitcoin private key cracking time to under 9 minutes
- Around $450B+ worth of BTC (6.7 million BTC) is potentially vulnerable
- Legacy Bitcoin address types (e.g., P2PK) are at highest risk
- Ethereum wallets may also be exposed within days under quantum attack scenarios
- Immediate migration to Post-Quantum Cryptography (PQC) is no longer optional—it is existential
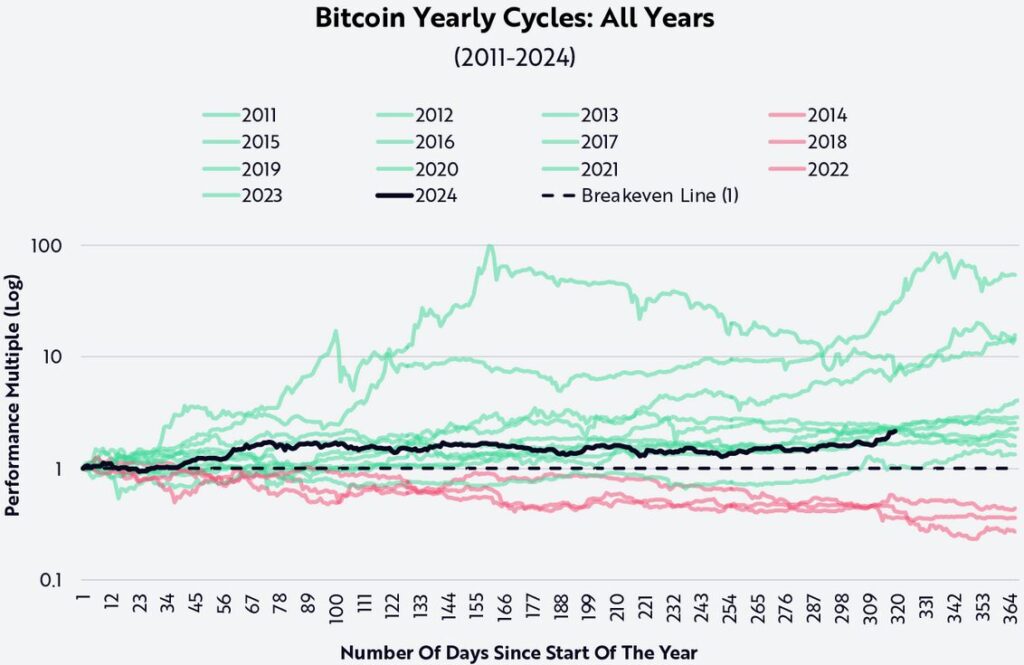
Bitcoin Price Volatility (2025–2026)
1. The Breakthrough: Google’s Quantum Leap in Cryptography
In March 2026, Google Research published a groundbreaking whitepaper that fundamentally reshapes the timeline for quantum cryptographic threats. The study demonstrated a dramatic reduction in the computational resources required to break ECDSA (Elliptic Curve Digital Signature Algorithm)—the cryptographic backbone of Bitcoin and many blockchain systems.
Previously, breaking ECDSA via quantum computing was considered a distant possibility, requiring millions of physical qubits and impractical error correction overhead. However, Google’s updated model estimates that only 1,200–1,450 logical qubits are needed—an order-of-magnitude improvement over prior assumptions.
More strikingly, Google chose to withhold critical circuit-level details, citing the potential for misuse. This marks a rare instance where a major research institution classifies portions of its findings due to security concerns—highlighting the seriousness of the breakthrough.
This is not merely theoretical progress. It represents a shift from “eventual possibility” to engineering inevitability.
2. From Theory to Reality: The 9-Minute Bitcoin Attack Scenario
Building upon Google’s findings, the cybersecurity research group Project Eleven applied the new quantum efficiency models to real-world blockchain conditions.
Their conclusion is alarming:
- A Bitcoin private key could be cracked in under 9 minutes
- Bitcoin’s average block time is approximately 10 minutes
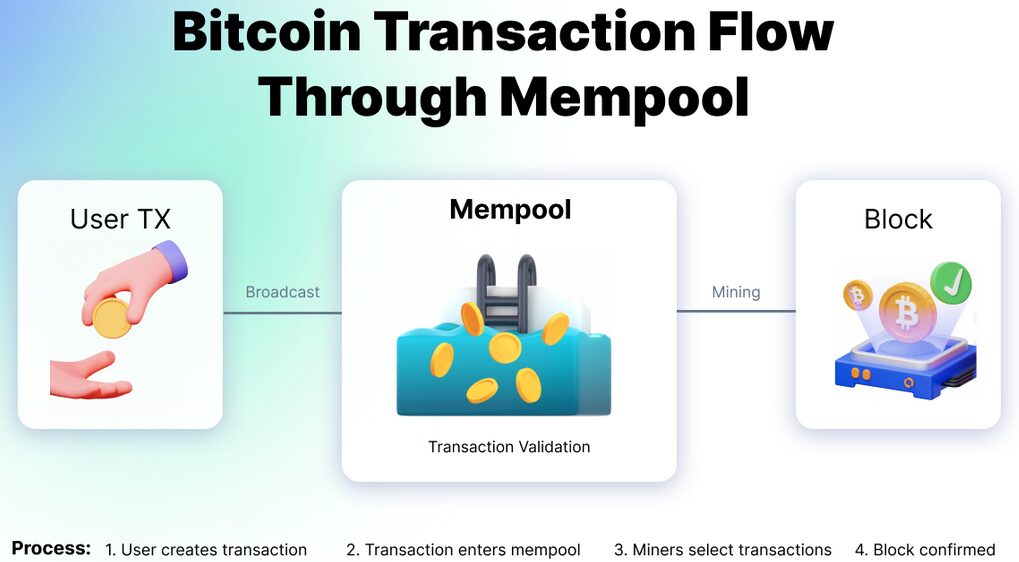
This creates a narrow but critical vulnerability window where attackers can intercept transactions in the mempool—the staging area for unconfirmed transactions.
This type of exploit, known as a mempool attack, was previously theoretical. Now, it becomes operationally plausible:
- A user broadcasts a transaction
- The public key becomes visible in the mempool
- A quantum attacker derives the private key within minutes
- The attacker replaces the transaction with a higher-fee version
- Funds are redirected before confirmation
This fundamentally undermines the assumption of transaction finality under current cryptographic guarantees.
3. The $450 Billion Exposure: Mapping Vulnerable Bitcoin Holdings

Using Google’s parameters, Project Eleven constructed a dataset called the “Bitcoin Risq List.”
Their findings:
- 6.7 million BTC exposed
- Equivalent to approximately $450 billion+ USD (assuming ~$67,000/BTC)
- Includes early-era wallets and inactive holdings
The most vulnerable category is P2PK (Pay-to-Public-Key) addresses—widely used in Bitcoin’s early days, including during the era of Satoshi Nakamoto.
Unlike modern address formats, P2PK addresses permanently expose the public key on-chain. This means:
- No transaction is required to reveal the key
- Attackers can begin quantum decryption immediately (at-rest attack)
Project Eleven estimates that approximately 1.7 million BTC fall into this high-risk category.
This is not just a security issue—it is a systemic concentration of dormant but vulnerable capital.
4. Ethereum and Beyond: A Multi-Chain Risk Landscape
The implications extend far beyond Bitcoin.
Project Eleven estimates that the top 1,000 wallets on Ethereum could be compromised within 9 days under similar quantum conditions.
While Ethereum uses different cryptographic structures, it still relies on elliptic curve cryptography, making it susceptible to quantum attacks.
Other affected ecosystems include:
- EVM-compatible chains (BNB Chain, Polygon, etc.)
- Layer 2 rollups
- Cross-chain bridges
- Custodial wallet infrastructures
This transforms quantum computing from a Bitcoin-specific concern into a universal blockchain risk vector.
5. Why This Matters Now: The Collapse of “Time Buffer” Assumptions
Historically, blockchain security has relied on a critical assumption:
Cryptographic systems will remain secure long enough to upgrade before being broken.
Google’s findings challenge this assumption directly.
The “time buffer” between theoretical vulnerability and practical exploitability is shrinking rapidly. In fact:
- Quantum hardware is scaling faster than expected
- Error correction techniques are improving
- Governments and private labs are investing billions
The implication is clear:
The transition window to quantum-resistant systems may already be open—and closing.
6. The Only Viable Defense: Post-Quantum Cryptography (PQC)
The recommended solution is Post-Quantum Cryptography (PQC)—algorithms designed to resist quantum attacks.
Key PQC approaches include:
- Lattice-based cryptography (e.g., CRYSTALS-Kyber, Dilithium)
- Hash-based signatures
- Multivariate polynomial cryptography
However, migrating blockchain systems to PQC is non-trivial:
Technical Challenges:
- Signature size increases (affecting block size and fees)
- Backward compatibility issues
- Hard fork requirements
- Wallet migration logistics
Governance Challenges:
- Community consensus
- Coordination across global nodes
- Handling dormant wallets (lost keys, inactive users)
Despite these hurdles, the alternative—inaction—is catastrophic.
7. Strategic Implications for Investors and Builders
For readers seeking new crypto assets and revenue opportunities, this shift creates both risks and opportunities:
Emerging Opportunities:
- PQC-native blockchains
- Quantum-secure wallets
- Cryptographic infrastructure providers
- Migration-as-a-service platforms
Strategic Positioning:
- Evaluate exposure to legacy wallet formats
- Monitor protocol-level PQC roadmaps
- Diversify into quantum-resilient ecosystems
Practical Considerations:
- Avoid reusing addresses unnecessarily
- Prefer modern address formats (e.g., P2WPKH, Taproot)
- Stay updated on client software upgrades
Quantum risk is no longer abstract—it is becoming a market differentiator.
8. Conclusion: A Defining Moment for Blockchain Survival
The convergence of Google’s research and Project Eleven’s applied analysis marks a turning point.
What was once theoretical is now actionable.
The blockchain industry faces a stark reality:
- Upgrade—or risk irreversible loss of trust
Unlike traditional systems, blockchains cannot easily recover from catastrophic breaches. Trust, once broken, cannot be restored through central intervention.
Therefore, the transition to PQC is not merely a technical upgrade—it is a civilizational requirement for decentralized finance.
The projects that act early will define the next era of crypto. Those that delay may not survive it.

