Main Points :
- A Russian intelligence–linked spy ring in the UK was funded through a sophisticated crypto-laundering network.
- The network was operated by Ekaterina Zhdanova, already sanctioned by the U.S., and involved conversion of illicit cash into untraceable cryptocurrency.
- Billions of dollars were routed through coin-laundering hubs in Moscow and Dubai.
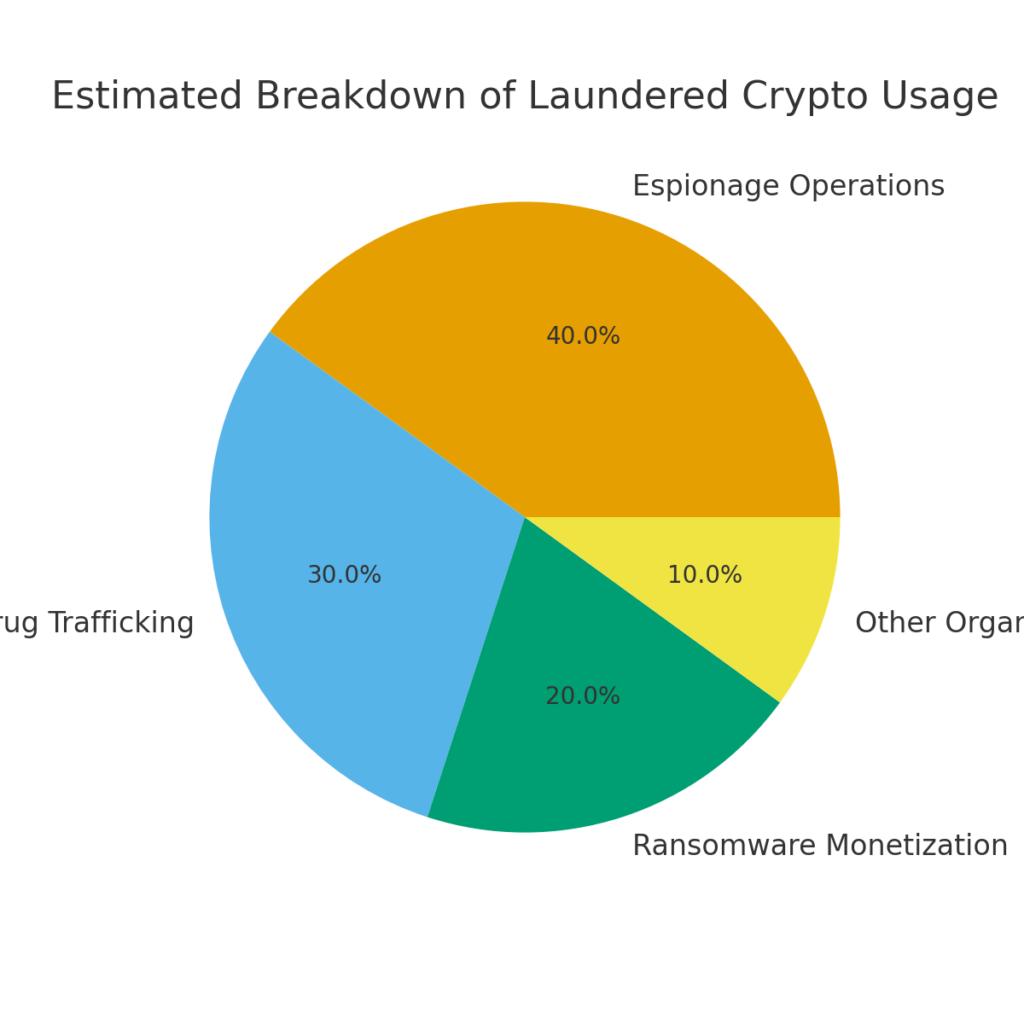
- The network supported espionage, ransomware monetization, and organized crime, spanning more than 30 countries.
- The case marks a new phase of global financial surveillance targeting crypto-based infrastructure tied to national security threats.
- Crypto laundering supported both Russian spy operations and UK-based drug organizations during the pandemic.
Introduction: A New Epoch in Crypto-Enabled Covert Warfare
In November 2025, the United Kingdom’s National Crime Agency (NCA) released explosive findings connecting Russian intelligence agencies to a vast crypto-based money-laundering infrastructure. This network channeled billions of dollars into covert operations—including espionage, political interference, assassination planning, and support for large-scale criminal enterprises.
The revelations mark a turning point in how digital assets intersect with national security. Rather than simply being used for cybercrime or ransomware payments, cryptocurrency has now been shown to underpin state-backed espionage operations with global reach.
For crypto investors and builders, this case highlights the strengthening regulatory spotlight on anonymity-enhanced transactions and cross-border flows. The greater the use of cryptocurrency in geopolitically sensitive contexts, the stronger—and more sophisticated—international oversight becomes.
Section 1 — The Network: How the Laundering System Worked
At the center of the NCA’s findings was a laundering ecosystem known informally as “Smart”, operated by Russian businesswoman Ekaterina Zhdanova. The system allowed criminals, oligarchs, and intelligence agencies to convert large amounts of physical cash into cryptocurrency that was extremely difficult to trace.
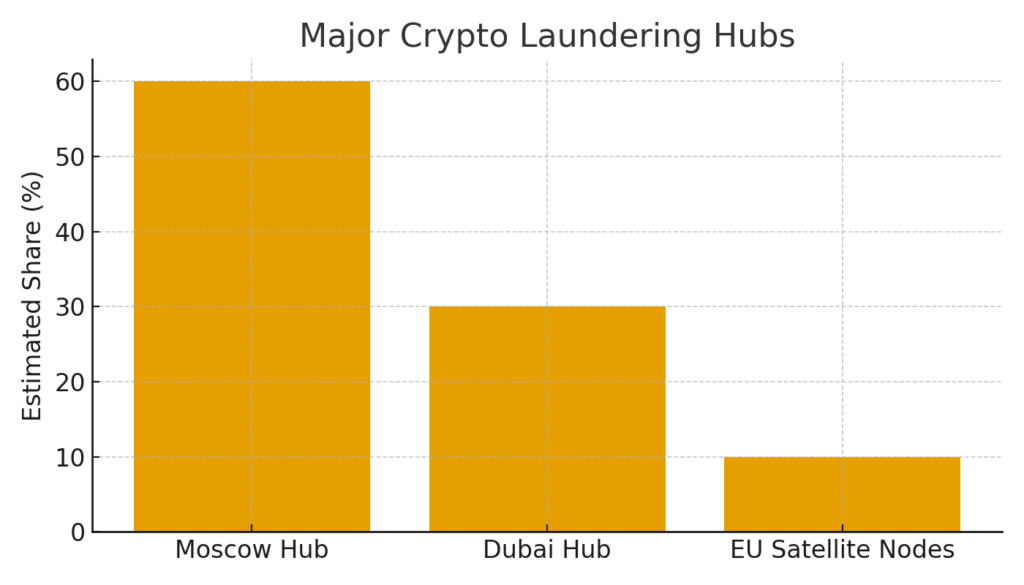
The NCA found that Moscow and Dubai hosted two of the largest crypto coin-laundering hubs in the world. These hubs acted as conversion and distribution centers for illicit funds moving across Europe, the Middle East, and Asia.
This laundering pipeline was used by:
- Russian intelligence agencies, to fund covert operations in the UK and EU.
- Jan Marsalek, the fugitive former Wirecard executive tied to Russian intelligence, who allegedly spent £45,000 (≈$57,000) on spy-related activities.
- UK-based criminal organizations, especially during pandemic lockdowns when physical cash movement became difficult.
- Ransomware groups, who needed a reliable pathway to convert digital extortion profits into usable fiat.
The sophistication of the system rivaled that of traditional offshore banking networks. Funds moved through:
- crypto OTC brokers in Dubai
- shell companies
- UK construction businesses used as laundering fronts
- networks spanning over 30 countries
This was not a single criminal group but a financial infrastructure—one that combined state actors and organized crime.
Section 2 — Russian Intelligence Operations Funded by Crypto
The laundering infrastructure enabled Russian agencies to support espionage activities inside the UK. According to the NCA, funds were used for:
- intelligence-gathering against journalists and politicians
- coordinated influence operations
- covert support for spy cells, including a six-member Bulgarian group convicted for espionage
- planning activities that included surveillance and potential assassinations
While many details remain classified, the NCA confirmed that cryptocurrency was essential in masking the movement of funds. Traditional wire transfers would have triggered early detection, but crypto networks allowed movements across borders with relative speed and lower visibility.
This case reveals how digital assets are now entrenched in global intelligence work—just as they transformed cybercrime over the past decade.
Section 3 — The Pandemic and the Rise of Criminal Crypto Flows
The NCA’s findings also revealed an unexpected pattern: UK criminal organizations, particularly drug distributors, increasingly relied on crypto conversion during pandemic lockdowns.
With movement restrictions blocking conventional cash-based laundering methods, syndicates adopted crypto at unprecedented scale. The same Russian laundering infrastructure became their preferred rail.
Authorities seized approximately £20 million (≈$25 million) in cash linked to £700 million (≈$890 million) in drug sales routed through these channels.
Organized crime, ransomware groups, and state-backed espionage actors were now using the same conversion infrastructure—a convergence that significantly complicates law enforcement.
Section 4 — Why This Case Matters for the Crypto Industry
This incident reflects the next stage of global regulatory evolution:
1. Crypto flows are now tied directly to national security
The UK’s report links digital assets to espionage and foreign interference—not just to financial crime.
2. Regulations will increasingly target unhosted wallets, mixers, and OTC brokers
The infrastructure used in this scheme relied heavily on non-KYC intermediaries and opaque OTC desks.
3. Travel Rule enforcement will intensify
Governments will push for near-real-time monitoring of high-risk cross-border transfers.
4. Exchanges and platforms must be prepared for intelligence-related inquiries
As state-actor usage rises, regulatory bodies will expect platforms to identify red-flag interactions tied to sanctioned individuals or geopolitical risks.
For builders and investors, understanding these trends is crucial. While the legitimate crypto ecosystem grows, so does the scrutiny of its darker edges.
Section 5 — Recent Developments (External Sources)
To place this case within the broader crypto landscape, several developments from late 2024–2025 are relevant:
Sanctions & AML tightening
- The U.S. Treasury expanded sanctions on Russian crypto OTC brokers, including entities in Dubai and Turkey.
- The EU implemented new AML rules targeting privacy coins and mixers.
Ransomware record highs
- 2024–2025 saw the highest ransomware payments in history, much of it funneled through crypto laundering services similar to Zhdanova’s network.
Middle East becoming a laundering hub
- Dubai grew into a major center for large-scale OTC operations, often operating in regulatory gray zones.
- Several exchanges were investigated for insufficient due-diligence controls.
Growing role of blockchain analytics
- TRM Labs, Chainalysis, and Elliptic advanced heuristics for tracing cross-chain laundering and identifying state-linked wallets.
- These tools were essential in unraveling the Russian networks.
Crypto’s value in illicit finance is not due to anonymity alone—but to speed, scalability, and borderlessness. As geopolitical tensions rise, crypto becomes an increasingly strategic financial tool for both legitimate and illicit actors.
Conclusion
The dissection of Russia’s crypto-laundering infrastructure marks a turning point in global financial governance. Cryptocurrency is no longer just a tool for speculative trading or cybercrime—it is part of the financial engine behind modern espionage and geopolitical conflict.
For the crypto industry, this case underscores a dual reality:
- Digital assets have become a core component of global finance, including sophisticated criminal and state operations.
- Regulators worldwide are entering an era of aggressive oversight, armed with more tools, more coordination, and more political backing than ever.
For entrepreneurs, investors, and developers, understanding this shift is not optional—it will define the regulatory environment of the next decade.
Infrastructure that prioritizes compliance, transparency, and traceability will not only survive but become critical to the future of legal digital finance.

