Key Points :
- A Solana-based DEX, Stabble, issued an emergency warning urging users to withdraw funds
- TVL dropped from $1.75M to under $663K (~62% decline) within days
- Suspicion centers on a former CTO allegedly linked to North Korean hacking groups
- Similar patterns seen in Drift Protocol exploit (~$285M loss)
- Highlights a growing trend: long-term infiltration rather than instant hacks
- Raises critical questions about insider risk, governance, and DeFi operational security
1. The Stabble Incident: A Sudden Collapse of Trust
What Happened?
In early April 2026, the Solana-based decentralized exchange Stabble issued an unprecedented alert to its users: withdraw all liquidity immediately.
This was not due to a confirmed exploit—but rather a high-risk internal threat.
The concern stemmed from allegations that a former Chief Technology Officer (CTO) may have been affiliated with North Korean cybercrime groups. While not yet fully confirmed, the risk level was deemed severe enough to trigger a platform-wide emergency response.
The market reacted instantly.
- TVL dropped from $1,750,000 → $663,000
- A loss of approximately 62% within a very short timeframe
This is not just a liquidity event—it is a confidence collapse.
TVL Collapse Visualization
2. A New Threat Model: Insider Infiltration vs External Exploits
Beyond Smart Contract Bugs
Historically, DeFi hacks were primarily:
- Smart contract vulnerabilities
- Oracle manipulation
- Flash loan exploits
However, the Stabble incident reflects a different class of threat:
Human-layer infiltration
Instead of attacking code, attackers may:
- Join as developers
- Gain privileged access
- Build trust over months
- Execute or prepare for large-scale compromise
This mirrors state-level cyber tactics rather than traditional hacking.
The North Korean Playbook
North Korean hacking groups (often associated with the Lazarus Group) have evolved significantly:
- Long-term infiltration (6–12 months)
- Fake identities and resumes
- Participation in legitimate development work
- Gradual access escalation
The suspected Stabble case aligns with this pattern.
3. The Drift Protocol Case: A $285M Warning Sign
A Precedent in the Same Ecosystem
Just days before the Stabble incident, another Solana-based platform, Drift Protocol, experienced a major exploit.
- Estimated loss: $285,000,000
- Suspected cause: multi-month infiltration strategy
Reports suggest attackers spent over six months preparing the attack, embedding themselves into operational processes.
Attack Timeline Illustration
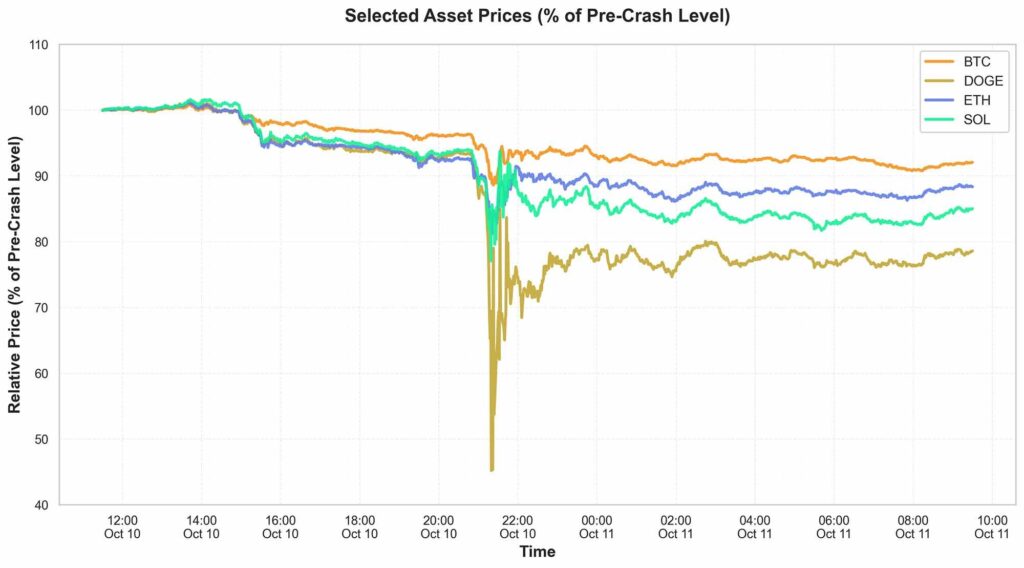
4. Market Impact: Liquidity Is Trust
Why TVL Matters
In DeFi, Total Value Locked (TVL) is not just a metric—it represents:
- User confidence
- Protocol credibility
- Market depth
A drop from $1.75M to $663K signals:
- Immediate withdrawal behavior
- Fear-driven decision-making
- Breakdown of trust in governance
Liquidity Flight Dynamics
The Stabble case demonstrates a classic DeFi panic pattern:
- Risk signal appears
- Early adopters withdraw
- Liquidity providers follow
- Slippage increases
- Remaining users exit
This creates a self-reinforcing collapse loop
5. Strategic Implications for Builders and Investors
For Builders (DEX / Wallet / Infrastructure)
This incident is directly relevant to your current architecture (especially given your hybrid DEX model):
Critical Controls to Implement
1. Developer Trust Framework
- Background verification (multi-layer)
- Git access segmentation
- Code ownership tracking
2. Privilege Minimization
- No single-point admin access
- Multi-signature approvals
- Time-locked upgrades
3. Behavioral Monitoring
- Developer activity logs
- Unusual access detection
- Insider threat analytics
4. Immutable Audit Trails
- All admin actions logged
- On-chain + off-chain correlation
- Forensic readiness
For Investors and Liquidity Providers
New Evaluation Criteria
When assessing DeFi opportunities:
- Who controls the codebase?
- Is governance truly decentralized?
- Are there insider risk protections?
- How transparent is team identity?
The risk is no longer just technical—it is organizational.
6. Emerging Trend: From DeFi to “TrustFi”
The Evolution of Security Expectations
We are entering a new phase:
| Phase | Risk Type | Mitigation |
|---|---|---|
| Early DeFi | Smart contract bugs | Audits |
| Mid DeFi | Economic attacks | Tokenomics |
| Current | Insider infiltration | Governance + Identity |
Trust as a Protocol Layer
Future successful protocols will likely include:
- On-chain identity verification
- Reputation systems
- Zero-trust development environments
- Continuous monitoring
This aligns with your Two-Extremes Model:
- Asset-backed representation (regulated trust)
- Autonomous trust (decentralized execution)
The challenge is bridging both safely.
7. Practical Takeaways for Your Current System Design
Given your work on:
- Non-custodial wallet
- On-chain matching (XXI Network)
- Hybrid DEX model
Immediate Recommendations
1. Separate Matching vs Control
- Matching engine: decentralized
- Admin controls: strictly governed
2. Introduce “Suspicious Developer Mode”
- Freeze high-risk functions
- Alert liquidity providers
- Trigger automatic safeguards
3. User-Level Safety Features
- Emergency withdrawal UI
- Risk notification system
- Transparency dashboards
Conclusion: The Real Risk Is Not Code—It’s Trust
The Stabble incident is not just about a $1M liquidity drop.
It represents a fundamental shift in how DeFi systems are attacked:
- From code vulnerabilities
- To human vulnerabilities
The implications are profound:
- Even audited code can be compromised
- Even decentralized systems can have centralized failure points
- Even trusted teams can become attack vectors
For builders, the lesson is clear:
Security must extend beyond the blockchain—into people, processes, and governance.
For investors:
Yield is meaningless without trust.

