
Main Points :
- The U.S. Treasury sanctioned six individuals and two companies connected to North Korea’s global IT worker fraud network.
- These workers allegedly generated over $800 million annually by secretly working for foreign companies using fake identities.
- Cryptocurrency—including Bitcoin ($BTC), Ethereum ($ETH), and Tron ($TRX)—was used to launder and move illicit funds.
- The U.S. added specific blockchain addresses to the OFAC SDN sanctions list, expanding enforcement to on-chain infrastructure.
- The case highlights a broader trend: nation-state cybercrime increasingly relies on crypto-based financial rails.
1. The Hidden Global Workforce Behind North Korea’s Revenue Strategy
In March 2026, the U.S. Department of the Treasury announced sanctions against six individuals and two companies connected to a global network of North Korean information-technology workers. According to the Office of Foreign Assets Control (OFAC), these individuals were part of a sophisticated scheme designed to generate foreign currency for the North Korean government while hiding their identities from employers and regulators.
The workers allegedly posed as freelance developers, engineers, and software specialists. They used stolen identities or fake profiles to secure remote employment with companies in the United States and other countries. Once hired, they transferred the majority of their earnings back to North Korea. Authorities believe these funds helped finance programs related to weapons of mass destruction and ballistic missile development.
The scale of the operation is significant. According to Treasury estimates, the scheme generated approximately $800 million in revenue in 2024 alone, making it one of the most lucrative cyber-enabled financial pipelines associated with the North Korean state.
The strategy itself is not entirely new. North Korea has long relied on overseas workers to generate foreign currency. However, the digital transformation of the global economy—especially the rise of remote work and freelance development platforms—has dramatically expanded the potential scale of such operations.
Platforms like remote developer marketplaces, coding communities, and outsourcing networks provide an environment where workers can collaborate anonymously across borders. For a state actor seeking covert revenue streams, this ecosystem provides a perfect opportunity.
From the perspective of international security agencies, the North Korean IT worker network represents a hybrid model of cybercrime and economic espionage. It blends traditional employment structures with digital deception, creating a pipeline that is difficult for regulators to detect.
2. Cryptocurrency as the Financial Infrastructure of Illicit Networks
A critical component of the operation involved cryptocurrency transactions.
According to the Treasury Department, several actors involved in the network converted earnings into digital assets to avoid traditional financial surveillance. One example highlighted in the investigation involved a company operating in Vietnam that allegedly helped convert funds into cryptocurrency between 2023 and 2025.
Authorities estimate that over $2.5 million was converted into cryptocurrency through these channels, including funds generated by fraudulent IT employment schemes.
Unlike traditional banking systems, cryptocurrency networks operate without centralized intermediaries. While blockchain transactions are publicly visible, the pseudonymous nature of wallet addresses makes attribution difficult without advanced analytics.
In this case, the U.S. government identified specific wallet addresses associated with the operation and placed them on the Specially Designated Nationals (SDN) sanctions list.
This is a significant development.
Historically, sanctions targeted individuals, companies, or financial institutions. Increasingly, however, governments are sanctioning digital wallet addresses themselves, effectively extending regulatory authority into blockchain infrastructure.
This trend reflects a growing recognition that digital assets have become a core component of global financial networks—including illicit ones.
Graph 1 — Estimated Revenue Sources of North Korean Cyber Operations
The chart above illustrates how North Korea’s cyber-enabled revenue ecosystem has diversified. While large cryptocurrency thefts remain prominent, IT worker schemes are emerging as a reliable source of steady income.
Some estimates suggest North Korean cyber actors stole over $2 billion in cryptocurrency in 2025 alone, highlighting how digital assets have become deeply integrated into geopolitical financial strategies.
3. From Fake Identities to Corporate Network Access
The threat posed by these workers goes beyond financial fraud.
In several documented cases, North Korean developers embedded malware into corporate networks or attempted to exfiltrate sensitive data. Because these workers often held legitimate remote positions within companies, they had access to internal systems, development environments, and sometimes proprietary intellectual property.
Security researchers have warned that such operations blur the line between economic infiltration and cyber espionage.
For example, previous investigations revealed that North Korean operatives created shell companies in the United States to lure developers and infiltrate cryptocurrency projects. These fake firms used fraudulent job postings to infect applicants’ computers with malware designed to steal credentials and digital wallets.
This tactic demonstrates a layered strategy:
- Generate revenue through legitimate-looking employment.
- Gather intelligence from corporate networks.
- Potentially deploy malware to steal additional cryptocurrency assets.
In effect, the same infrastructure used to generate income can also be used for cyber-espionage operations.
4. The Expanding Role of Sanctions in Crypto Regulation
The inclusion of cryptocurrency wallet addresses in the sanctions list highlights a major shift in regulatory strategy.
Under U.S. law, entities listed on the SDN list are effectively cut off from the global financial system. Financial institutions must block transactions involving these entities, and U.S. citizens are prohibited from conducting business with them.
By adding blockchain addresses to the SDN list, the U.S. government is sending a clear signal to cryptocurrency exchanges, wallet providers, and decentralized finance platforms.
They are expected to screen blockchain transactions in the same way banks screen wire transfers.
OFAC has already published guidance explaining that digital asset transactions are subject to the same sanctions compliance requirements as fiat currency transfers.
In practice, this means that:
- Exchanges must monitor blockchain addresses for sanctions exposure.
- Crypto companies must implement transaction screening tools.
- DeFi protocols face increasing pressure to incorporate compliance mechanisms.
This development reflects a broader regulatory evolution.
Cryptocurrency was originally promoted as a borderless financial system independent of government oversight. Yet the increasing use of digital assets in cybercrime, ransomware, and sanctions evasion has pushed regulators to extend enforcement into blockchain infrastructure.
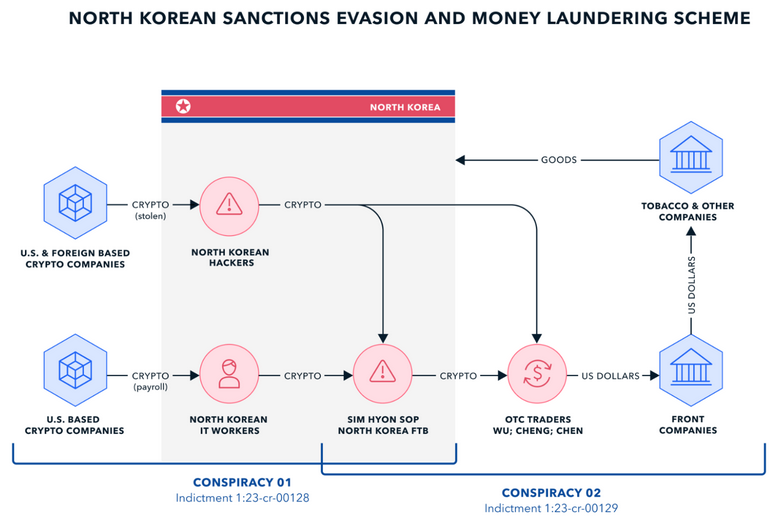
Diagram 2 — Typical Crypto Laundering Flow Used in State-Sponsored Cybercrime

Typical laundering pipelines involve several steps:
- Earnings or stolen funds are received in cryptocurrency wallets.
- Assets are transferred through multiple intermediary wallets.
- Funds may pass through mixers or cross-chain bridges.
- Finally, assets are converted to fiat currency through exchanges or OTC brokers.
By sanctioning wallet addresses early in this process, regulators hope to disrupt the financial infrastructure that supports these operations.
5. What This Means for the Crypto Industry
For cryptocurrency businesses and investors, the sanctions highlight several key trends shaping the future of the industry.
First, blockchain analytics is becoming an essential compliance tool. Companies increasingly rely on data platforms that track wallet clusters, transaction patterns, and risk indicators.
Second, regulatory scrutiny of crypto-enabled financial crime is intensifying worldwide. Governments are expanding legal frameworks that apply traditional financial regulations to digital assets.
Third, the geopolitical dimension of cryptocurrency is becoming more visible. Digital assets are no longer just speculative investment instruments—they are also tools used by states, intelligence agencies, and criminal networks.
For blockchain developers, this environment presents both challenges and opportunities.
On one hand, compliance requirements may increase operational complexity. On the other hand, the demand for security solutions, blockchain analytics tools, and identity verification systems is rapidly growing.
Projects that can provide trust infrastructure—such as decentralized identity systems, compliance-friendly DeFi protocols, and secure digital payment rails—may play an increasingly important role in the next phase of blockchain adoption.
Conclusion
The latest sanctions targeting North Korea’s IT worker network highlight a fundamental shift in the intersection between geopolitics, cybersecurity, and cryptocurrency.
What once appeared to be isolated cybercrime incidents are now understood as components of a broader financial strategy employed by nation-states. Remote employment fraud, cyber espionage, and digital asset laundering are all part of an integrated ecosystem designed to generate revenue and bypass international sanctions.
For regulators, the response is clear: expand enforcement into the blockchain ecosystem itself.
For the cryptocurrency industry, the implications are equally significant. The future of digital assets will likely be shaped not only by technological innovation, but also by how effectively the industry can prevent abuse by state-sponsored actors.
As governments continue to track illicit financial flows across blockchain networks, the line between decentralized finance and global regulatory systems will continue to evolve.

