Key Points :
- Quantum computing risk to Bitcoin has been reassessed as “manageable,” not existential by Bernstein
- The timeline has shortened to 3–5 years, driven by new research from Google
- The biggest vulnerability lies in legacy wallets from the Satoshi Nakamoto era
- Migration to post-quantum cryptography (PQC) will likely be gradual and costly (billions to trillions USD)
- Institutional players like BlackRock and Fidelity Investments may play a critical role in securing the ecosystem
- Mining remains largely immune to quantum threats in practical terms
- The industry faces a trade-off between security upgrades and network efficiency
Introduction
The emergence of quantum computing has long been regarded as a distant but existential threat to blockchain technology, particularly Bitcoin. However, recent developments have significantly reshaped this narrative. A report by Bernstein has reframed the risk—not as an immediate collapse scenario, but as a manageable, structured transition over the coming years.
This shift is largely driven by new findings from Google, which suggest that the quantum resources required to break Bitcoin’s cryptographic protections may be lower than previously estimated. As a result, the timeline for potential disruption has been compressed from over a decade to approximately three to five years.
Yet, this compression does not necessarily translate into panic. Instead, it introduces a new phase of strategic adaptation, where blockchain ecosystems, developers, and institutional investors must coordinate a phased migration toward quantum-resistant architectures.
The Compression of the Quantum Timeline
From Decades to Years
Historically, quantum threats to Bitcoin were considered a long-term concern—something for future generations of developers to address. However, recent research by Google indicates that breaking Bitcoin’s ECDSA signatures may require around 500,000 qubits, significantly lower than earlier estimates in the millions.
This finding has triggered a reassessment across the industry. Bernstein now acknowledges that what was once a distant threat may materialize within 3–5 years.
Why This Still Isn’t Immediate
Despite the alarming reduction in theoretical requirements, practical implementation remains a major hurdle. Quantum systems must still overcome:
- Error correction challenges
- Hardware scalability limitations
- Manufacturing constraints
These obstacles suggest that real-world quantum attacks may still lag behind theoretical breakthroughs.
Quantum Threat Timeline
Where the Real Risk Lies: Legacy Wallets
The Vulnerability of Early Bitcoin Addresses
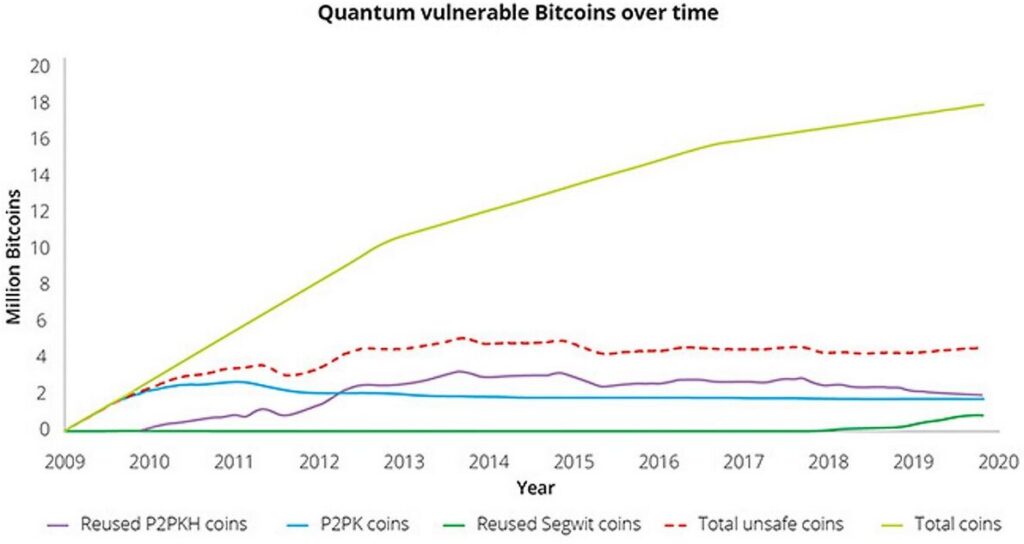
The most critical exposure lies in early Bitcoin wallets, particularly those associated with the era of Satoshi Nakamoto. These wallets often have public keys already exposed on-chain, making them susceptible to a “store now, decrypt later” attack.
An estimated 1.7 million BTC fall into this category—representing tens of billions of dollars in potential risk (≈ $100B+ depending on market price).
Modern Wallets: Safer by Design
In contrast, newer wallet architectures only reveal public keys upon transaction execution, significantly reducing exposure. This design inherently mitigates quantum risks—at least for now.
Institutional Capital as a Security Driver
The Role of Large Financial Players
The transition to quantum-resistant systems is not just a technical challenge—it is a capital-intensive one. Estimates suggest migration costs could reach hundreds of billions to trillions of USD.
This is where institutions such as BlackRock, Fidelity Investments, and Coinbase become crucial.
For example:
- Coinbase has already formed a quantum advisory council
- Asset managers are expected to fund infrastructure upgrades
- Custodians will drive wallet migration standards
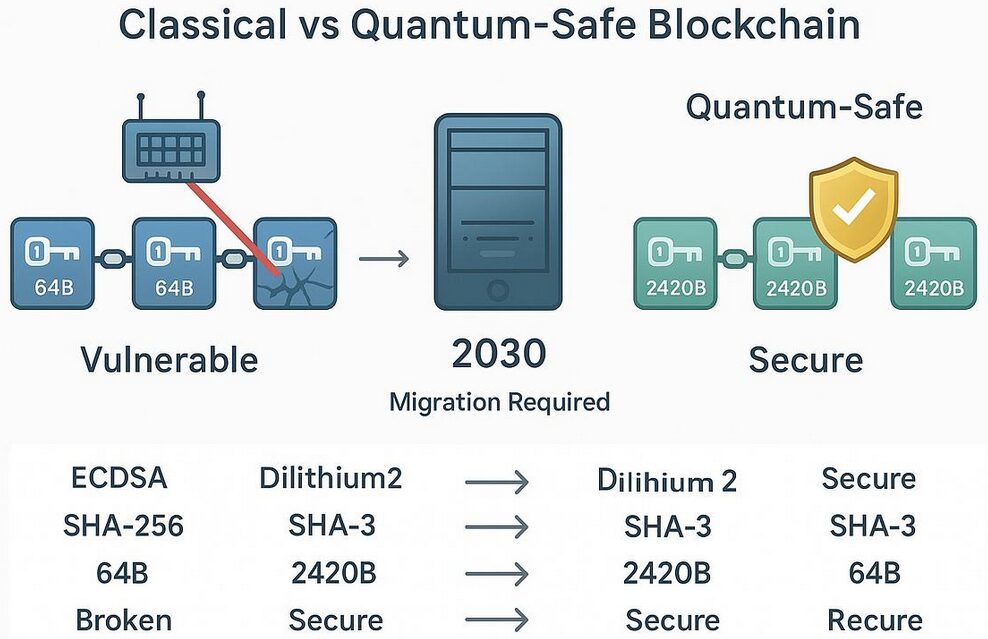
Migration Architecture to Post-Quantum Cryptography
Mining and Quantum Resistance
SHA-256 and Grover’s Algorithm
Bitcoin mining relies on SHA-256 hashing, which could theoretically be accelerated by Grover’s algorithm. However, this only provides a quadratic speedup, not an exponential one.
In practical terms, executing such an attack would require energy comparable to the output of the sun, rendering it effectively impossible.
Shor’s Algorithm and Reality
While Shor’s algorithm poses a real threat to cryptographic signatures, its application to mining would require millions of years of computation with current projections.
Conclusion: Mining is not the weak point. Wallet cryptography is.
The PQC Trade-Off: Security vs Performance
The Hidden Cost of Safety
Transitioning to post-quantum cryptography introduces new challenges:
- Signature sizes may increase 10x to 125x
- Network throughput could decline
- Storage and bandwidth requirements will rise
Industry figures like Samson Mow have warned that rushed adoption could trigger a new “block size war.”
Risk of Overcorrection
Ironically, premature migration may introduce new vulnerabilities in classical computing environments. This creates a delicate balance between:
- Acting too late (quantum risk)
- Acting too early (system instability)
Industry Voices and Strategic Outlook
Conservative but Prepared
Leaders such as Adam Back emphasize that current quantum computers remain primitive, far from threatening Bitcoin in practice.
At the same time, proactive measures are already underway:
- Gradual wallet migration strategies
- Development of PQC standards
- Institutional coordination
Strategic Implications for Investors and Builders
For Investors
- Legacy Bitcoin holdings may carry hidden quantum risk premiums
- Institutions investing in infrastructure may gain long-term advantage
- New quantum-resistant chains could emerge as alternative assets
For Builders
- Wallet design must prioritize quantum agility
- Layered security models will become standard
- Interoperability with PQC systems will be critical
Conclusion: A Managed Evolution, Not a Crisis
The narrative around quantum computing and Bitcoin is evolving from fear to strategy. While the timeline has undeniably shortened, the consensus among leading analysts and industry participants is clear: this is not an existential crisis, but a managed technological transition.
The next three to five years will be defined by coordination—between developers, institutions, and users. Success will depend not on avoiding quantum disruption entirely, but on navigating it intelligently.




