Key Points :
- Ethereum developers launched a Post-Quantum Resource Hub to prepare for quantum threats
- Protocol-level quantum resistance targeted by 2029 with phased implementation
- No immediate threat, but early coordination is critical due to system complexity
- Debate continues: only exposed wallets vs. all crypto assets at risk
- Integration of SNARKs (zero-knowledge proofs) to mitigate performance degradation
- Migration challenge: upgrading hundreds of millions of wallets safely
- Broader industry trend: quantum risk becoming a strategic priority across crypto ecosystems
1. Introduction: Why Quantum Computing Matters for Blockchain
The rise of quantum computing represents one of the most profound technological shifts of the 21st century. While still in its early stages, the theoretical capability of quantum computers to break classical cryptographic systems has triggered growing concern across industries—especially within blockchain ecosystems that rely heavily on cryptographic security.
Ethereum, one of the world’s largest blockchain platforms with tens of billions of dollars in value secured on-chain, has now taken a decisive step. By launching a dedicated “Post-Quantum Ethereum” initiative, developers are signaling that the future of blockchain security must be built today—not when the threat becomes imminent.
This proactive approach reflects a broader realization: in decentralized systems, delayed action is not an option.
2. Ethereum’s Post-Quantum Initiative: Structure and Timeline
The Ethereum developer community, supported by the Ethereum Foundation, has introduced a structured roadmap to transition the network toward quantum resistance.
Planned Timeline
- 2025–2027: Research, cryptographic evaluation, and testing
- 2027–2029: Protocol-level integration of quantum-resistant algorithms
- Post-2029: Expansion into execution and application layers
The newly formed Post-Quantum team is not only focused on selecting cryptographic primitives but also on building a comprehensive resource hub. This hub serves as a coordination layer for developers, researchers, and ecosystem participants.
A key message from the team is clear:
The absence of an immediate threat does not justify inaction.
Because Ethereum is a global, decentralized protocol, any upgrade requires years of coordination, formal verification, and staged deployment. This makes early preparation not just beneficial—but necessary.
3. The Quantum Threat Debate: Real or Overstated?
The crypto industry remains divided on the urgency and scope of quantum risk.
On one side, analysts argue that only wallets with exposed public keys are vulnerable. In Ethereum and Bitcoin-like systems, public keys are typically revealed only after a transaction is made, limiting exposure.
On the other hand, more cautious experts suggest that all cryptographic assets may eventually be at risk, particularly if quantum computing progresses faster than expected.
Key Risk Vectors
- Private key derivation from public keys
- Signature forgery
- Smart contract vulnerabilities
- Long-term stored assets (cold wallets)
Even if large-scale quantum computers remain years away, the “harvest now, decrypt later” attack model presents a real concern. Attackers could collect encrypted blockchain data today and decrypt it in the future once quantum capabilities mature.
4. Technical Strategy: SNARKs and Performance Preservation
One of the central challenges in implementing quantum-resistant cryptography is performance degradation.
Post-quantum algorithms often require:
- Larger key sizes
- Higher computational overhead
- Increased bandwidth and storage
To address this, Ethereum developers are exploring the integration of SNARKs (Succinct Non-Interactive Arguments of Knowledge).
Why SNARKs Matter
- Compress large proofs into small, verifiable data
- Reduce on-chain data requirements
- Maintain scalability despite heavier cryptographic operations
This hybrid approach—combining post-quantum cryptography with zero-knowledge proofs—represents a cutting-edge architectural strategy. It aims to ensure that security enhancements do not come at the cost of usability or network efficiency.
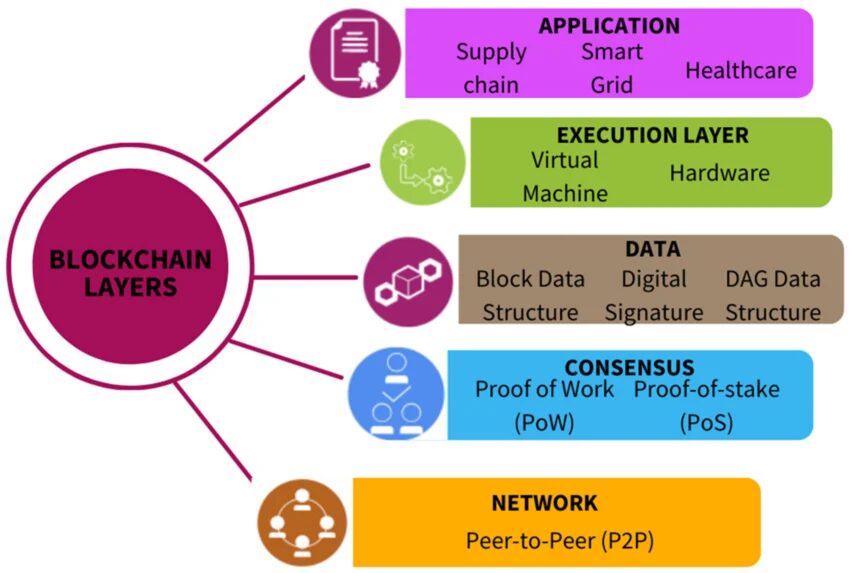
5. Multi-Layer Implementation: Consensus, Execution, Data
Ethereum’s upgrade strategy spans all core layers of the blockchain:
Consensus Layer
- Validator signatures
- Block validation security
Execution Layer
- Smart contract interactions
- Transaction processing
Data Layer
- Storage integrity
- Historical data protection
This full-stack approach ensures that quantum resistance is not a patch—but a foundational redesign of security assumptions.
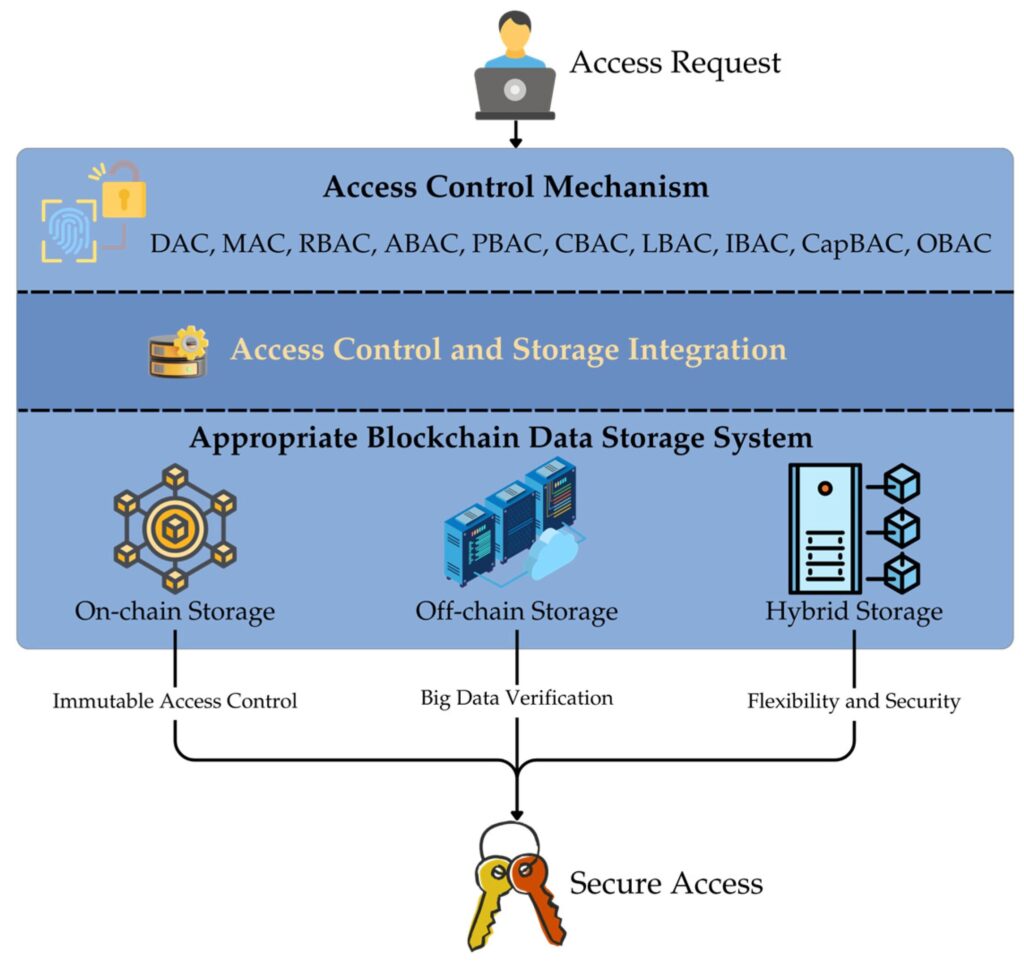
6. Migration Challenge: Upgrading Hundreds of Millions of Wallets
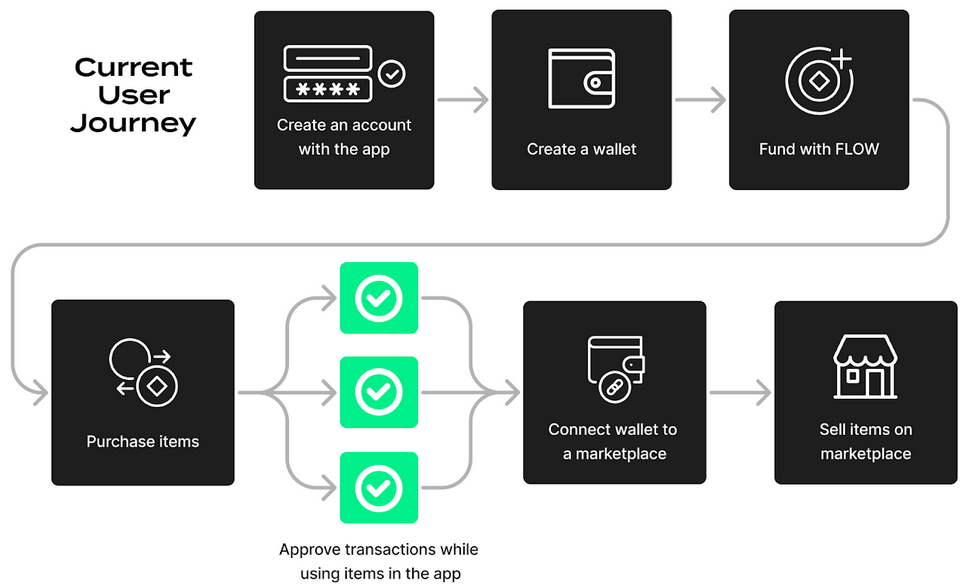
Perhaps the most difficult aspect of this transition is not technical—it is operational.
Ethereum must safely upgrade:
- Hundreds of millions of user accounts
- Institutional wallets (exchanges, custodians, bridges)
- Smart contracts and DeFi infrastructure
Key Challenges
- Avoiding network disruption
- Preventing new vulnerabilities during migration
- Ensuring backward compatibility
- Coordinating across global participants
The prioritization strategy reflects risk exposure:
- Standard user wallets
- High-value institutional wallets
- Infrastructure-level components
This staged approach reduces systemic risk while maintaining network continuity.
7. Broader Industry Implications: A New Security Paradigm
Ethereum is not alone in this shift.
Across the crypto ecosystem:
- Bitcoin developers are exploring post-quantum signature schemes
- Governments are funding quantum-resistant cryptography research
- Financial institutions are preparing for post-quantum compliance frameworks
This indicates a broader transition toward what can be called:
“Quantum-Aware Blockchain Architecture”
For investors and builders, this shift creates new opportunities:
- Development of quantum-resistant protocols
- Security-focused infrastructure startups
- Cross-chain migration tools
- Advanced wallet technologies
8. Investment and Strategic Opportunities
For readers seeking new revenue streams and practical blockchain applications, the post-quantum transition opens several avenues:
Emerging Opportunities
- Post-quantum cryptography libraries and SDKs
- Zero-knowledge infrastructure providers
- Secure custody solutions for long-term assets
- Quantum risk analytics platforms
Market Insight
The transition to quantum-resistant systems may trigger:
- Capital rotation into “future-proof” assets
- Increased valuation for security-focused projects
- Regulatory incentives for compliant infrastructure
This is not merely a technical upgrade—it is a market-defining transformation.
9. Conclusion: Building Before the Storm
Ethereum’s post-quantum initiative represents a rare example of long-term thinking in a fast-moving industry.
Rather than reacting to immediate threats, the ecosystem is preparing for a structural shift in computational reality.
The key takeaway is simple:
The future of blockchain security will not be decided when quantum computers arrive—but by the preparations made years in advance.
For investors, developers, and institutions alike, the message is clear:
Quantum resilience is no longer optional—it is inevitable.




