Key Points :
- A UK-based investor claims his estranged wife stole 2,323 BTC (~$176 million) using surveillance footage to capture a seed phrase.
- Funds were moved across 71 addresses, highlighting advanced obfuscation tactics.
- The case underscores the critical vulnerability of seed phrase exposure, even in hardware wallets.
- Legal proceedings suggest a high likelihood of recovery or favorable judgment, but enforcement remains uncertain.
- Broader concerns include dusting attacks, privacy risks, and operational security failures in crypto self-custody.
- The incident reflects a growing trend: human-layer attacks are replacing technical hacks as the primary threat vector.
1. A $176 Million Bitcoin Theft: What Happened?
In one of the most unusual yet instructive cryptocurrency cases in recent years, a UK-based investor, Pin Fai Yuen, has filed a lawsuit against his estranged wife, accusing her of stealing 2,323 BTC—valued at approximately $176 million at current market prices.
According to court filings, the alleged theft occurred in 2023 and involved a Trezor hardware wallet, typically considered one of the safest storage methods for digital assets. However, the breach did not involve software vulnerabilities or hacking tools. Instead, it exploited a far more fragile layer: human security.
The plaintiff claims that his wife, along with her sister, used hidden surveillance cameras to capture the wallet’s seed phrase and access credentials. With this information, they allegedly transferred the Bitcoin into 71 separate wallet addresses, effectively fragmenting the funds to reduce traceability.
What makes this case particularly notable is that no further transactions have been recorded since December 21, 2023, suggesting either strategic dormancy or fear of detection.
Bitcoin Flow Fragmentation (Illustration of 71 Address Distribution)
2. The Real Weakness: Seed Phrase Exposure
This case reinforces a fundamental truth in crypto security:
Your seed phrase is your wallet.
Even the most secure hardware wallet becomes irrelevant once the seed phrase is exposed. Unlike traditional banking systems, there is:
- No password reset
- No fraud reversal
- No central authority
Once compromised, ownership is effectively transferred.
In this case, the attacker did not need to hack the device. Instead, they leveraged:
- Physical proximity
- Behavioral observation
- Covert recording
This type of attack falls under what security experts call “side-channel attacks” or “human-layer attacks.”
Attack Vector Comparison (Technical Hack vs Human Exploit)
3. Legal Perspective: High Probability of Plaintiff Victory
The UK High Court has already indicated that the plaintiff has a “strong likelihood of success.”
Key factors include:
- Recorded conversations discussing the theft
- Lack of alternative explanation from the defendant
- Physical evidence recovered during police searches
The court has also emphasized urgency, citing:
- Bitcoin’s volatility
- Risk of further transfers
- Difficulty of asset recovery
However, even if the plaintiff wins legally, enforcement remains a separate challenge.
The Core Problem:
Crypto ownership is determined by private keys, not court orders.
Unless authorities can:
- Access the wallets
- Seize the private keys
- Or compel disclosure
Recovery may remain partial or delayed.
4. Dormant Funds and Blockchain Forensics
Interestingly, the stolen Bitcoin has not moved since late 2023. This creates two possible scenarios:
Scenario A: Strategic Dormancy
The attacker is waiting for:
- Reduced attention
- Legal resolution
- Better laundering opportunities
Scenario B: Lost or Frozen Access
Possible complications:
- Multi-signature errors
- Key mismanagement
- Law enforcement pressure
Blockchain forensic firms (e.g., Chainalysis, TRM Labs) often monitor such wallets continuously.
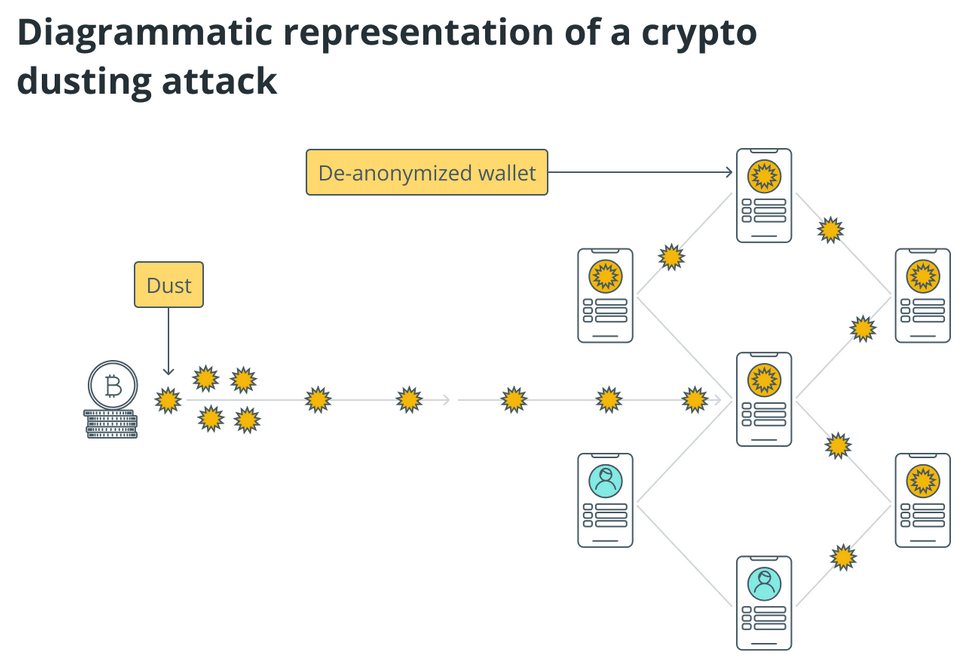
5. The Emerging Threat: Dusting Attacks
The plaintiff has raised concerns about dusting attacks targeting the stolen addresses.
What is a Dusting Attack?
A dusting attack involves sending tiny amounts of cryptocurrency to multiple wallets to:
- Track wallet behavior
- Link identities
- Identify large holders (whales)
Once identified, attackers may launch:
- Phishing attacks
- Blackmail attempts
- Social engineering campaigns
Dusting Attack Mechanism
6. Broader Industry Trend: Human Attacks Are Rising
This case is not isolated. Across the crypto industry, a clear shift is emerging:
Old Threat Model:
- Smart contract hacks
- Exchange breaches
New Threat Model:
- Seed phrase theft
- Social engineering
- Insider attacks
Recent reports indicate that over 60% of major crypto thefts now involve human factors, not technical exploits.
7. Practical Lessons for Investors and Builders
For your audience—those seeking new crypto opportunities and practical blockchain applications—this case provides critical lessons:
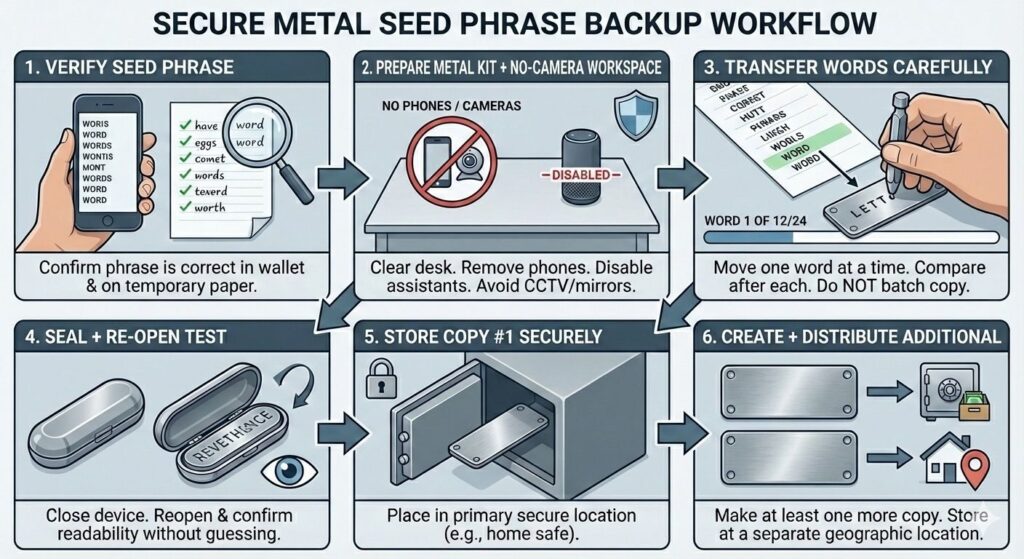
1. Never Digitize Your Seed Phrase
- No photos
- No cloud storage
- No screenshots
2. Avoid Single Point of Failure
- Use multi-signature wallets
- Separate key storage locations
3. Physical Security Matters
- Treat seed phrases like cash or gold
- Control access to your environment
4. Consider Institutional Custody
For large holdings:
- MPC (Multi-Party Computation)
- Custodial vaults
- Insurance-backed solutions
5. Monitor On-Chain Activity
- Use blockchain analytics tools
- Set alerts for wallet movements
8. Strategic Insight: The Future of Self-Custody
This incident raises a deeper question:
Is full self-custody still viable for high-net-worth individuals?
We are seeing a hybrid future emerge:
- Retail users → simplified self-custody
- High-value holders → institutional-grade security layers
This aligns with your broader thesis:
The convergence of “Autonomous Trust Tender” and “Asset-Backed Representation”
Where:
- Pure decentralization meets
- Structured, secure financial systems
Conclusion
The alleged theft of 2,323 BTC (~$176 million) is not just a legal dispute—it is a case study in the evolution of crypto risk.
It demonstrates that:
- The weakest point in crypto security is often human behavior
- Legal systems are still adapting to decentralized asset ownership
- Advanced attacks now focus on psychology, proximity, and process—not code
For investors and builders alike, the message is clear:
The future of crypto security will not be won by better code alone—but by better systems, better habits, and better operational design.




