Main Points :
- A sophisticated cyberattack targeting multiple cryptocurrency companies may be linked to North Korean hacking groups.
- Attackers exploited vulnerabilities in staking service websites to infiltrate backend systems.
- Sensitive data—including wallet private keys, API credentials, and infrastructure configuration files—was stolen.
- Cloud service credentials (AWS) were abused to access internal corporate systems.
- Exchange infrastructure software from blockchain service provider ChainUp was reportedly exfiltrated.
- No immediate asset theft was detected, but the stolen information could enable future large-scale attacks.
- The attack resembles past supply-chain intrusions attributed to the North Korean cyber group TraderTraitor.
- The incident highlights a growing trend: state-sponsored actors targeting crypto infrastructure rather than just wallets.
Introduction: Cyber Warfare Enters the Infrastructure Layer of Crypto
The global cryptocurrency industry has spent years strengthening its defenses against exchange hacks and wallet thefts. Yet a recent cybersecurity report suggests that attackers—possibly linked to North Korea—have begun targeting a far deeper layer of the ecosystem: the infrastructure that powers crypto exchanges and staking services themselves.
According to a report released by the security research organization Ctrl-Alt-Intel, a coordinated cyber campaign infiltrated multiple cryptocurrency companies, exploiting web vulnerabilities and compromised cloud credentials to steal sensitive data, including backend code and authentication keys.
While no immediate loss of funds has been confirmed, investigators warn that the stolen information may represent preparation for future large-scale asset theft. For investors, developers, and institutions entering the blockchain space, this incident serves as a stark reminder that the security battle around digital assets is rapidly evolving.
Exploiting Web Vulnerabilities in Staking Platforms
The attack reportedly began with a common yet dangerous entry point: website vulnerabilities in cryptocurrency staking service providers.
Staking platforms—services that allow users to deposit tokens in exchange for yield—have become an increasingly important part of the crypto economy. However, their complex backend systems often interact with wallets, smart contracts, and financial infrastructure simultaneously, making them attractive targets for hackers.
According to the investigation, attackers successfully exploited weaknesses in the target company’s website. Through this entry point, they gained access to backend systems where critical components of the staking infrastructure were hosted.
Once inside the system, the hackers extracted several categories of high-value data, including:
- Backend application code
- Wallet private keys
- System configuration files
- Internal service credentials
The theft of wallet private keys is particularly alarming, as such information can potentially enable attackers to sign transactions or gain control of digital assets in the future.
Although no immediate theft has been reported, security experts emphasize that compromised keys often remain dormant until attackers find the optimal moment to exploit them.
Cloud Credential Abuse: AWS Access Opens the Internal Network
In addition to exploiting web vulnerabilities, the attackers reportedly obtained credentials for cloud services—specifically Amazon Web Services (AWS).
Cloud environments play a central role in modern crypto infrastructure. Exchanges, blockchain analytics systems, trading engines, and API gateways frequently run on cloud-based architecture.
Using compromised AWS authentication credentials, attackers were able to access internal systems belonging to the targeted organizations. From there, they systematically harvested sensitive information stored within the cloud environment.
Stolen information reportedly included:
- Database connection credentials
- API keys for internal services
- Infrastructure configuration files
- Data used by infrastructure management tools
The attackers also examined configuration files and management tools stored in the cloud environment, suggesting a methodical effort to map the internal architecture of the companies involved.
This type of reconnaissance is typical in advanced persistent threat (APT) operations, where attackers study infrastructure for weeks or months before launching a financially motivated attack.
Exchange Software Theft: The ChainUp Supply-Chain Risk
One of the most concerning findings from the report involves the theft of exchange infrastructure software provided by ChainUp, a global blockchain technology company that supplies exchange software to many crypto trading platforms.
According to the investigation, attackers successfully obtained copies of the exchange software used by one of ChainUp’s customers.
The problem lies in how some exchange software is deployed: in certain cases, database access credentials may be embedded within configuration files or application code.
If attackers gain access to these credentials, they may be able to:
- Access exchange databases
- Manipulate trading records
- Interfere with internal systems
- Potentially execute asset withdrawals
This represents a classic supply-chain attack scenario, where compromising a software provider or shared infrastructure component allows attackers to target multiple downstream platforms simultaneously.
The report suggests that the affected platform was a customer of ChainUp, rather than the software provider itself.
Nevertheless, the incident demonstrates how interconnected the crypto ecosystem has become—and how vulnerabilities in one layer can affect multiple companies.
Infrastructure Obfuscation: Korean Servers and VPN Routing
Investigators also discovered that the attackers routed their operations through servers located in South Korea and used Korean VPN services to mask their activity.
Such techniques are frequently used by advanced cybercriminal groups to make attribution more difficult.
By routing traffic through different geographic regions, attackers can obscure their origin and delay forensic analysis by cybersecurity teams.
While the infrastructure appears to be based in Korea, investigators believe the servers were likely used purely as relay nodes, rather than indicating the true location of the attackers.
Possible Link to North Korean Hacker Groups
Although the report stops short of making a definitive attribution, researchers state that the attack has moderate confidence links to North Korean threat actors.
The reasoning behind this assessment includes several similarities to previous attacks associated with North Korean cyber units.
Notably, the techniques used in the incident resemble those seen in the 2025 Bybit hack, one of the largest cryptocurrency security breaches in recent years.
Investigators also note similarities to operations conducted by the North Korean hacking group TraderTraitor, which has previously targeted technology companies and cryptocurrency platforms.
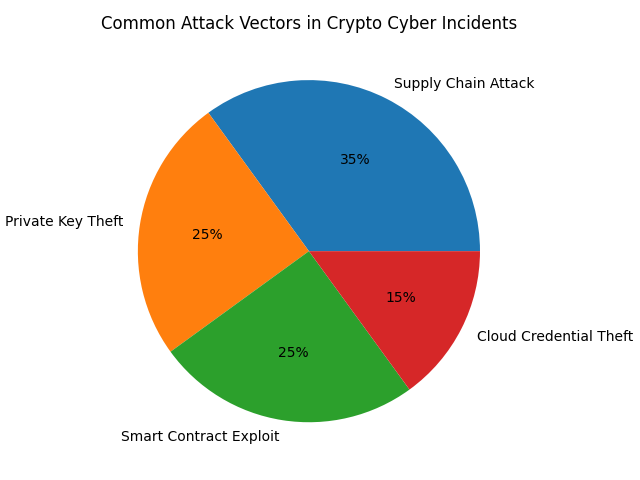
TraderTraitor has been associated with several supply-chain attacks, including:
- The JumpCloud breach (2023)
- Cryptocurrency exchange intrusions
- Infrastructure infiltration campaigns
These operations typically focus on stealing credentials, source code, and internal system information before launching financially motivated attacks later.
North Korea’s Crypto Strategy: Financing Through Cybercrime
North Korea has long been suspected of using cybercrime to fund its economy and strategic programs.
Blockchain analysis firms such as Chainalysis and TRM Labs have repeatedly reported that state-linked hackers from North Korea are responsible for billions of dollars in cryptocurrency theft.
Some of the most well-known incidents include:
- The Ronin Bridge hack (2022) — $625 million stolen
- The Harmony Horizon bridge hack (2022) — $100 million stolen
- The Atomic Wallet exploit (2023) — $100 million stolen
- The Bybit incident (2025) — a major exchange breach
These attacks often involve sophisticated techniques such as:
- Supply-chain infiltration
- Social engineering of developers
- Malware targeting crypto wallets
- Compromised infrastructure access
The latest incident suggests that attackers are shifting focus from direct wallet theft toward systematic infiltration of crypto infrastructure.
The Industry Response: Strengthening Security Architecture
As the cryptocurrency industry matures, security practices are also evolving.
Exchanges and infrastructure providers are increasingly implementing:
- Hardware security modules (HSMs) for key management
- Multi-party computation (MPC) wallets
- Zero-trust network architecture
- Infrastructure segmentation
- Continuous threat monitoring
Cloud security is becoming especially important, as many crypto companies rely heavily on AWS, Google Cloud, or other providers.
Best practices now emphasize:
- Strict IAM access control
- Key rotation policies
- Secrets management systems
- Infrastructure monitoring
For companies building staking platforms, DeFi protocols, or exchanges, the attack serves as a reminder that web applications and cloud configurations remain critical security layers.
What This Means for Investors and Builders
For readers searching for the next crypto investment opportunity or exploring practical blockchain use cases, cybersecurity is becoming an increasingly important factor in evaluating projects.
Investors are now paying close attention to whether platforms implement:
- Professional security audits
- Transparent infrastructure architecture
- Strong key management systems
- Incident response plans
Projects that demonstrate strong operational security may gain a competitive advantage as institutional capital flows into the digital asset market.
At the same time, infrastructure providers—rather than just token projects—may become attractive opportunities for builders and investors.
Companies offering:
- Secure wallet infrastructure
- MPC key management
- blockchain security analytics
- decentralized custody systems
are seeing growing demand across the industry.
[“Major Cryptocurrency Hacks by Value (2022-2025)”]
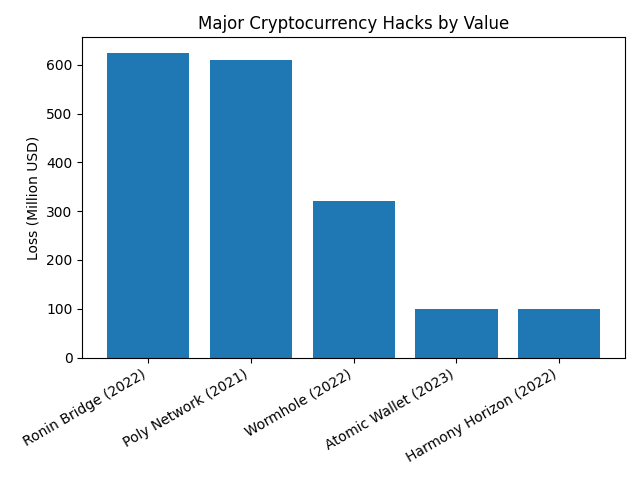
Suggested data visualization:
- Ronin Bridge Hack — $625M
- Poly Network Hack — $610M
- Wormhole Bridge Hack — $320M
- Atomic Wallet Hack — $100M
- Bybit Incident — Estimated hundreds of millions
(Graph should illustrate the increasing scale of crypto security incidents.)
The Future of Crypto Security
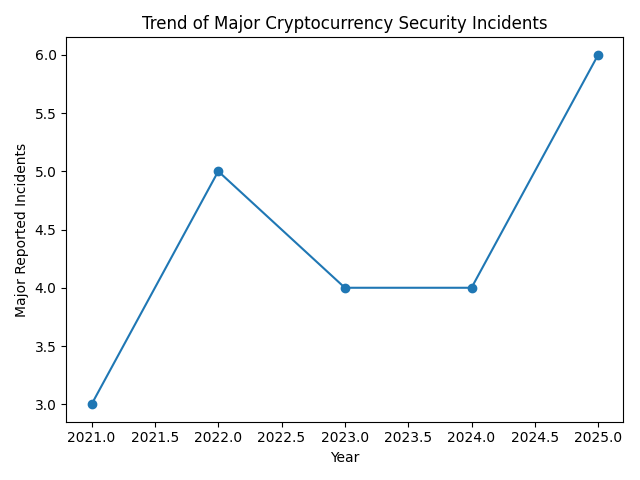
The incident described in the report may represent a new phase in cyber warfare targeting digital assets.
Rather than immediately stealing funds, attackers appear to be collecting intelligence and preparing access for future operations.
This strategy aligns with long-term cyber espionage tactics commonly used by state-linked threat actors.
As the crypto economy grows into a multi-trillion-dollar financial ecosystem, it will likely remain a major target for sophisticated attackers.
Conclusion
The reported cyber campaign targeting cryptocurrency companies highlights a critical shift in how attackers approach the digital asset industry.
Instead of focusing solely on stealing funds from wallets or exploiting smart contracts, threat actors are increasingly targeting infrastructure layers, including cloud systems, backend applications, and exchange software.
While no direct asset loss has been confirmed in this incident, the stolen data—including private keys, API credentials, and exchange software—could potentially enable large-scale attacks in the future.
For the crypto industry, the lesson is clear: security must extend beyond blockchain protocols to encompass the entire technology stack supporting digital assets.
As institutional adoption accelerates and new blockchain applications emerge, companies that prioritize robust cybersecurity architecture will be best positioned to thrive in the next phase of the crypto economy.